- Educate all business staff about dangers and latest attack methods, particularly ensuring they aware of targeted scam emails (spear phishing). Cyber criminals are increasingly targeting individual business staff members, typically those with finance responsibilities, by crafting highly convincing emails using information about the business, its staff and its suppliers. These scam emails once responded to, will typically try to convince (social engineer) individual staff members to arrange a bank transfer or payment to a bogus account operated by the cyber criminals
- Keep all Servers, PCs, Laptops, Tablets and Smart Phones operating systems and applications updated (security patching). Out of date software is vulnerable and commonly exploited by malware and hackers.
- Business staff should use unique passwords with each third party/online service used by the business. Ensuring passwords are complex and changed every 90 days. Where possible use mutli-factor authentication (I.e. password + hardware token or text message confirmation). Cyber criminals know many people use the same email and password combination across multiple websites, so when they obtain one credentials combination, usually via a third party website hack, the database of which are often dumped onto the darkweb, cyber criminals try the same stolen email and password combinations to attempt to access further online services, with the intent of stealing personal data and money.
UK cybersecurity analysis, operational resilience, control assurance, AI security, and evidence-based governance from experienced practitioners and guest contributors.
 More from Cybersecurity Expert
Practitioner-led cybersecurity analysis, AI Labs tools, book updates and evidence-based assurance thinking.
Visit the website
Explore AI Labs
Read about the book
More from Cybersecurity Expert
Practitioner-led cybersecurity analysis, AI Labs tools, book updates and evidence-based assurance thinking.
Visit the website
Explore AI Labs
Read about the book
21 December 2016
How to Protect your Business from Cyber Crime
Today I was quoted in the Focus Training's Blog. An 'Ask the Experts' piece on 'How to Protect your business from Cyber Crime', my advice was as follows.
20 December 2016
UK Identity Fraud on the Rise
UK identity fraud is on the rise according to the latest research by Equifax. The data shows UK ID crime is going up within all age groups, with those living in the London and Manchester areas increasingly the most likely to become victims of ID fraud. Equifax has asked me to share the following infographic on their research, which includes good advice to stay protected.
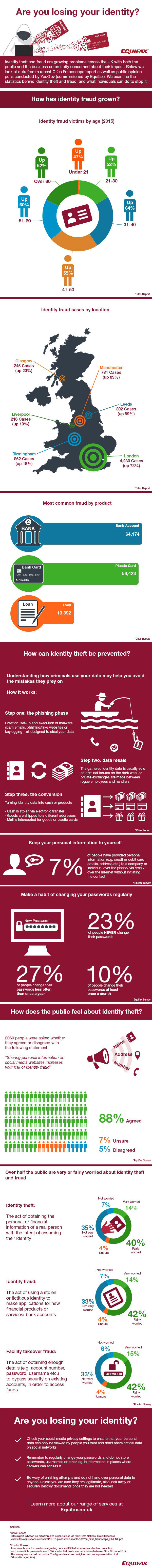
Are you losing your identity? We look at the growth of identity fraud and what can be done about it
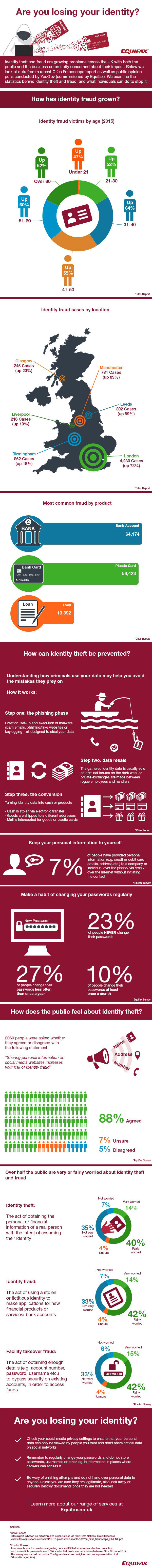
Are you losing your identity? We look at the growth of identity fraud and what can be done about it
15 December 2016
Yahoo's Mind-blowing One Billion Data Theft Hack
Just over three months ago I posted about Yahoo, The Largest Data Breach in History...so far. It was apt I added "so far" in the post title as in the early hours today, Yahoo announced an even more mind-blowing data theft hack of over One Billion Yahoo user accounts.
If you are a concerned Yahoo email account holder
The latest reports say that Yahoo lost data for more than one billion users back in August 2013 and that the data is suspected to contain names, email addresses, hashed passwords, security questions and associated answers. In addition, Yahoo has stated that the attackers have accessed Yahoo proprietary code used to generate cookies for user access without credentials.
This breach raises a number of questions, including: Why did it take so long to identify and notify authorities about it? What are the implications for Yahoo users? What might this mean for Yahoo going forward?
Yahoo appears to have been informed by law enforcement that the breach may have occurred, indicating that its internal detective controls have been, and may continue to be, inadequate. This is reinforced by a statement from Bob Lord (Yahoo's CISO) who stated "we have not been able to identify the intrusion associated with this theft." (https://yahoo.tumblr.com/post/154479236569/important-security-information-for-yahoo-users).
Although Yahoo claims that this notification is distinct from the 2014 breach (reported in September 2016), it raises questions as to why this more significant breach was not identified during earlier investigations. Forensic investigations may have been either too focussed on the 2014 breach, or incomplete, preventing identification of this earlier and more significant breach. To add balance to this argument, it should be stated that it is not clear at this time if the breached systems were related, however following the 2014 breach, Yahoo should certainly have considered further investigations to identify if any wider breaches had occurred.
So what are the implications for Yahoo users? Considering that this breach constitutes approximately one-third of Yahoo’s user base, it would be a fair assumption for all Yahoo users that their accounts have been compromised. The data set reported to be compromised includes both username and passwords, and whilst the passwords are reportedly hashed, the weak algorithm in use leaves them wide open to abuse (see our earlier blog post on password hashing - https://www.cyberis.co.uk/2012/06/adding-pinch-of-salt.html)
Cyberis advises Yahoo users, and users of related services such as Flickr and Tumblr, to change their passwords with immediate effect. If you have used your Yahoo password with any other service, you should also change these passwords. If you have registered for a website using a Yahoo email account, you should also consider resetting your password for these services, especially if you haven't used them for some time. Password reset services often use email addresses to manage a password change or forgotten password function. Anyone with access to the breached data could have potentially used this information to access any site associated with your Yahoo email account.
Given that Yahoo has announced that proprietary data was accessed, the breach is currently assumed to extend to Yahoo internal systems. This could suggest a highly skilled and motivated adversary, potentially even a state-sponsored hacking group. Access to millions of email accounts would be a clear motivation to many different threat actors of course, including foreign intelligence services and governments. We fully expect that further information about the extent of the breach will be released in the near future, but in the meantime, it’s certainly not looking good for Yahoo.
If you are a concerned Yahoo email account holder
1. Reset your Yahoo account password, make sure your old Yahoo passwords are not used on any other of your online accounts
2. Change your Security Questions and Answers on all accounts with same Q&A as Yahoo, you might have to make up false answers only you know to ensure safety
3. Be extra vigilant, especially with signs of any access to your email account, and receiving scam phishing emails
Mark Crowther, Associate Director at Cyber Security Specialists Cyberis (www.cyberis.co.uk), has some interesting thoughts on the latest breach at Yahoo, raising serious questions about the company's historical and ongoing security programme. The following are his views.
The latest reports say that Yahoo lost data for more than one billion users back in August 2013 and that the data is suspected to contain names, email addresses, hashed passwords, security questions and associated answers. In addition, Yahoo has stated that the attackers have accessed Yahoo proprietary code used to generate cookies for user access without credentials.
This breach raises a number of questions, including: Why did it take so long to identify and notify authorities about it? What are the implications for Yahoo users? What might this mean for Yahoo going forward?
Yahoo appears to have been informed by law enforcement that the breach may have occurred, indicating that its internal detective controls have been, and may continue to be, inadequate. This is reinforced by a statement from Bob Lord (Yahoo's CISO) who stated "we have not been able to identify the intrusion associated with this theft." (https://yahoo.tumblr.com/post/154479236569/important-security-information-for-yahoo-users).
Although Yahoo claims that this notification is distinct from the 2014 breach (reported in September 2016), it raises questions as to why this more significant breach was not identified during earlier investigations. Forensic investigations may have been either too focussed on the 2014 breach, or incomplete, preventing identification of this earlier and more significant breach. To add balance to this argument, it should be stated that it is not clear at this time if the breached systems were related, however following the 2014 breach, Yahoo should certainly have considered further investigations to identify if any wider breaches had occurred.
So what are the implications for Yahoo users? Considering that this breach constitutes approximately one-third of Yahoo’s user base, it would be a fair assumption for all Yahoo users that their accounts have been compromised. The data set reported to be compromised includes both username and passwords, and whilst the passwords are reportedly hashed, the weak algorithm in use leaves them wide open to abuse (see our earlier blog post on password hashing - https://www.cyberis.co.uk/2012/06/adding-pinch-of-salt.html)
Cyberis advises Yahoo users, and users of related services such as Flickr and Tumblr, to change their passwords with immediate effect. If you have used your Yahoo password with any other service, you should also change these passwords. If you have registered for a website using a Yahoo email account, you should also consider resetting your password for these services, especially if you haven't used them for some time. Password reset services often use email addresses to manage a password change or forgotten password function. Anyone with access to the breached data could have potentially used this information to access any site associated with your Yahoo email account.
Given that Yahoo has announced that proprietary data was accessed, the breach is currently assumed to extend to Yahoo internal systems. This could suggest a highly skilled and motivated adversary, potentially even a state-sponsored hacking group. Access to millions of email accounts would be a clear motivation to many different threat actors of course, including foreign intelligence services and governments. We fully expect that further information about the extent of the breach will be released in the near future, but in the meantime, it’s certainly not looking good for Yahoo.
01 December 2016
Cyber Security Roundup for November 2016
Several major UK household brands made the headlines for wrong reasons following cyber attacks in October. Tesco Bank refunded £2.5 million to over 20,000 of its customers after Tesco Bank account credentials were hacked and account funds were stolen. Mobile giant ‘Three’ said 6 million of its customer’s personal data records could be at risk after hundreds of new mobile phones were stolen following the hack of a Three employee account. The National Lottery disclosed 26,500 of its online customer accounts had been accessed by hackers, leading to three arrests. Elsewhere a 17 year old pleaded guilty to taking part in the recent TalkTalk hack.
The next evolution of ransomware has arrived with a new variant called Ransoc, and it's pretty nasty. The malware scans internet history, social media accounts, Skype and photos, and then uses any found illegal, embarrassing and sensitive information to threaten the victim’s reputation should a payment not be sent.
It turns out locked computer desktops aren’t as safe as you might think after a security researcher Samy Kamar released details of new attacking method called PoisonTap. Samy is famous for hacking MySpace with a worm way back in the day, I had the pleasure of meeting him a few years ago - An Evening with Samy, creator of the Samy MySpace Worm. In simple terms PoisonTap works by plugging a £4 Raspberry Pi Zero computer configured with hacking tools into a USB port, forcing the USB port to act as a network port, the tool is able to eavesdrop non-encrypted network traffic and steal web sessions from web browser sessions running in the background on PCs and Apple Macs, despite the desktop being locked with password protection. Samy released the source code for PoisonTap on Github, and I intend to create a PoisonTap tool for myself in the next few days.
News
- Tesco Bank Hack: £2.5m refunded to 20,000 Customers
- Three Data Breach Cyber Hack: Six Million Customers Data at Risk
- National Lottery Hack: 26,500 Players' Online Accounts Accessed
- Financial Conduct Authority rapped for Lack of Cyber Experts on Board
- Lincolnshire NHS Trust Operations cancelled after Cyber Attack
- Capgemini Leaks 780,000 Michael Page Job Candidate CVs
- UK iPhone users hit by large scale Smishing Campaign
- 17-year-old pleads guilty to offences linked to TalkTalk Hack
- European Commission gets DDoSed
- Hackers hit San Francisco transport Systems
- Bruce Schneier: ‘The internet era of fun and games is over'
- Microsoft release 6 Critical Patches for Windows, Edge, IE, Video Control & Flash
Awareness, Education and Intelligence
- NIST Releases CyberSecurity Guide for Small Businesses
- New Ransomware Variant Extorts your Reputation rather than Money
- PoisonTap: £4 Tool which can hack locked PCs via a USB Port
- YouTubers sell Phishing Kits in Plain View
- Cerber Ransomware: Now with Database Encryption
- Facebook spam caught delivering Locky Ransomware
17 November 2016
"Hacked Again" by Scott N Schober - Book Review
I have just finished reading the book "Hacked Again" by US CyberSecurity Expert Scott Schober. Along with covering and explaining several recent major hacks, the book provides excellent advice and tips for staying safe from cyber crime.
What I found particularly interesting was Scott's own account on how he was hacked. As CEO of his own successful Wireless Security company and a popular Cyber Security TV pundit, I imagine Scott's natural instinct would be to not disclose his "been hacked" experience with the world. Scott disregards any potential embarrassment to himself and chooses to explain what exactly happened to him and why, passing on valuable lessons learnt to help others, a brave and noble undertaking I applaud.
What "Hacked Again" is, is a potent reminder that no one is ever safe from the clutches of persistent cyber criminals. But this doesn't mean we should give up trying to be secure, on the contrary, as following the practical advice given in the book significantly reduces your chances of becoming a victim of cybercrime.
Hacked Again is available from Amazon as a Hardback, Paperback, Kindle or an Audiobook.
What I found particularly interesting was Scott's own account on how he was hacked. As CEO of his own successful Wireless Security company and a popular Cyber Security TV pundit, I imagine Scott's natural instinct would be to not disclose his "been hacked" experience with the world. Scott disregards any potential embarrassment to himself and chooses to explain what exactly happened to him and why, passing on valuable lessons learnt to help others, a brave and noble undertaking I applaud.
What "Hacked Again" is, is a potent reminder that no one is ever safe from the clutches of persistent cyber criminals. But this doesn't mean we should give up trying to be secure, on the contrary, as following the practical advice given in the book significantly reduces your chances of becoming a victim of cybercrime.
Hacked Again is available from Amazon as a Hardback, Paperback, Kindle or an Audiobook.
15 November 2016
Stay Safe from Cyber Crime - Top Ten Tips InfoGraphic
Given I am regularly asked to explain cyber attacks and then advise on how to protect against them, particularly to home users of late, I thought I would try my hand at creating a simple InfoGraphic to help. It was a challenge to create due to the limitation to the amount of space for text, which means you can't cover everything and you can't go into much detail. However concise messaging is kind of the point of infographics, especially when using them as awareness tools.
This InfoGraphic is squarely aimed at the average "home user", it highlights what the bad guys are after, their most popular and most successful attack methods, and then provides 10 tips to help avoid and detect home user cyber attacks, simples.
If this InfoGraphic proves popular I'll create some more, starting with one covering home IoT Security advice, another subject I'm regularly asked about at the moment.

Download full version here
Labels:
cyber,
Fraud,
hackers,
Home Security,
ID Theft,
infographic,
malware,
Mobile Security,
Network Security,
password security,
Patching,
Payment Card Fraud,
ransomware,
Security Awareness,
Social Media,
Wifi Security
07 November 2016
Why a Cyber Attack can cost a Law Firm an Arm and a Leg
Law firms collect, process and store vast amounts of extremely sensitive data about their clients, this when combined with a poor 'people security' culture and a general lack of digital security know-how, is a recipe that leaves legal companies highly vulnerable to cyber attacks. Given the typical large scope and sensitivity of data held by law firms, cyber attacks in the legal industry can be particularly costly affairs to recover from. Often you will read about regulators imposing considerable data breach fines on companies that have been the subject of a cyber attack. Yet the hidden cost of a data breach recovery in using crisis management services, disruption of critical business operations, contractual penalties, bringing in forensic investigators, and engaging a legal counsel, ironic I know, and the loss of client trust often exceeds the financial penalty figures plastered across the headlines.
Emphasising the legal profession's vulnerability to cyber attacks, Logikcull, a provider of automated data discovery and management to the legal sector, have compiled an InfoGraphic of data breach statistics to highlight the issue, and tips to help safeguard data and prevent cyber attacks from being successful.

Via logikcull
Emphasising the legal profession's vulnerability to cyber attacks, Logikcull, a provider of automated data discovery and management to the legal sector, have compiled an InfoGraphic of data breach statistics to highlight the issue, and tips to help safeguard data and prevent cyber attacks from being successful.
Via logikcull
01 November 2016
Cyber Security Roundup for October 2016
Cyber security experts have long predicted that thousands of vulnerable Internet of Things (IoT) devices such as internet-connected CCTV systems would be hacked on mass and directed to perform huge DDoS attacks. That’s exactly what happened on 21st October when 152,000 IoT devices infected with malware were remote controlled by hackers and then used to orchestrate a 1Tb DDoS attack, the largest in history. A tsunami of network traffic was directed at a company called Dyn, a major domain name registrar, and it impacted their client’s web services, including Twitter, Yammer, PayPal, Starbucks, The Guardian, PlayStation, Wix, CNN, Spotify, Github, Weebly and Reddit.
Those IoT developers may want to read up on my IoT guidance on the IBM developersWorks website - Combating IoT cyber threats Top security best practices for IoT applications
The UK National Cyber Security Centre HQ went operational, which is part of the UK government's 5 year £1.9 billion cyber defence strategy, a much-needed investment to help safeguard the UK's digital economy from cyber attacks during these uncertain economic times for the country.
Ransomware continues to cause problems, especially within NHS, but on the flipside the https://www.nomoreransom.org/ website continues to be supported, with site providing excellent advice to both home users and businesses. I have even added a separate Ransomware Help section on my own website - https://itsecurityexpert.co.uk/en/securityhelp/ransomware-help
A couple of surveys show UK businesses are still struggling to understand what they need to do in order to comply with new strict General Data Protection Regulation (GDPR), which comes into force in May 2018 despite brexit. I plan to do a blog post providing business help the GDPR in the coming weeks.
News
- World Biggest DDoS attack blows away Dyn, impacting Twitter, Yammer, and others
- UK National Cyber Security Centre HQ Operational
- NHS Attacked by Ransomware 'Dozens' of Times
- 'Hackable' Apple watches banned from UK Government Cabinet meetings
- Hackers steal 43 million credentials from Weebly
- In wake of Massive Data Breach, Verizon reassessing price for Yahoo Acquisition
- Student discovers security flaw in Virgin Media Recruitment System
- MasterCard plans to authenticate transactions using Selfies
- European Ransomware initiative gains 13 new Member Countries
- Over £1 Billion Lost by UK businesses to Online Crime in the Last Year
- UK Banks not Reporting Cyber-Attacks
- Hackers hiding Stolen Credit Card Details in Images
- Forged Rail Tickets sold on 'Dark Web', BBC investigation reveals
- Microsoft bundles Security Updates - no more pick and choose
- Microsoft release 7 Critical Patches for Windows, Edge, IE, Office & Flash Player
- Throw your Backdoored D-Link DWR-932B Router in the bin, urges Security Researcher
Awareness, Education and Intelligence
Reports
- EU GDPR - Nine out of Ten Don't Understand it
- Thales Survey: 84% of Brits reconsider Brands affected by Data Breaches
- PCI SSC: The UK Business CyberSecurity Threat
- Mobile is the New Playground for Thieves: How to Protect against Mobile Malware
- 73% of organisations across the globe have suffered a DDoS attack – Neustar Study
- 82% of Global and IT business Pros are concerned about GDPR compliance
- Network Security Playbook Guide
Labels:
application security,
brexit,
CCTV,
cyber security roundup,
data breach,
Data Protection,
DDoS,
DPA,
Fraud,
GDPR,
Hacking,
ibm,
ICO,
iot,
malware,
Microsoft,
Patching,
PCI DSS,
ransomware,
yahoo
27 October 2016
How to Protect Against Mobile Malware
IBM Security recently released a white paper on the mobile malware threat, which included general guidance on managing the mobile threat and an overview of IBM’s MaaS360 Mobile Threat Management tool, I thought it was good advice and well worth sharing.
According to Arxan Technologies. 97% and 87%t of the top paid Android and iOS apps, respectively, have been hacked and posted to third-party app stores.
Mobile Security Guidance (by IBM Security)
- Educate Employees about Application Security: Educate employees about the dangers of downloading third-party applications and the potential dangers that can result from weak device permissioning.
- Protect BYOD devices: Apply enterprise mobility management capabilities to enable employees to use their own devices while maintaining organisational security.
- Permit Employees to download from Authorised App Stores Only: Allow employees to download applications solely from authorised application stores, such as Google Play, the Apple App Store and your organisation’s app store, if applicable.
- Act Quickly when a Device is Compromised: Set automated policies on SmartPhones and tablets that take automatic action if a device is found compromised or malicious apps are discovered. This approach protects your organisation’s data while the issue is remediated.
02 October 2016
Cyber Security Roundup for September 2016
The theft of
over half a billion Yahoo user accounts by hackers has dominated the news
headlines in the last couple of weeks. Since announcing the largest hack in
history, Yahoo has come in for heavy criticism, given it took two years for
Yahoo to notice the massive data theft, talk of lacklustre security behind the
scenes at the company, and doubts over Yahoo’s claims the cyber attack was
state-sponsored. Lawyers representing users, the US Senate and the UK ICO have
all lined up to take pop-shots at Yahoo and are threatening action.
Interesting example of Hacktivism after a Russian group called "Fancy Bears" hacked and released the World Anti-Doping Agency medical records of prominent British and American Olympic athletes. The motivate appears to be a revenge protest aimed at causing embarrassment to medal winning Western athletes following the banning of several Russian athletes at the recent Rio Olympic games for banned sport enhancing drug use. The posted stolen records showed western athletes had taken a variety of banned drugs for legitimate reasons and conditions, which all were approved by the Anti-Doping Agency. Fascinating case for both athletics and data protection worlds, as even athletes in the public eye still have a right to privacy, especially when it concerns information about any medical conditions they have.
UK payment card fraud has risen by 53% over the last 12 months. The shock increase was blamed on scammers using more sophisticated attack methods. This spike in payment card fraud certainly would have been noted by the UK National Cyber Security Centre (NCSC), as it gears up to launching next month. The NCSC is part of the UK government’s £1.9 billion investment plan to beef up the UK’s cyber security capabilities over the next 5 years.
There is an
interesting video webinar posted this month, which reviews the $81 million
SWIFT Bank Hack by the company that investigated it. It concludes with the
SWIFT Bank investigators firmly pointing the finger of blame at weak endpoint
security at the bank. Elsewhere the Locky Ransomware continues to be evolved by
hackers seeking to make their fortune out of the nefarious tool.
On Tuesday 27th September I spoke at the R3 Summit (Resilience, Response and Recovery) in London, and summarised my advised approach with cyber incident management in a blog post the following day - Cyber Security Incident Management, Response and Recovery Guidance
News
- Yahoo Hit in Worst Hack Ever, Over 500 Million Accounts Stolen
- World Anti-Doping Agency Medical records released by Russian Hackers
- Payment Fraud soars by 53% in a year as scammers get Sophisticated
- TalkTalk loses appeal against £1000 ICO Penalty
- UK moves to ‘Active Cyber-Defence’ as the NCSC Gears Up
- GCHQ to fund startups to fight Cyber-Crime
- Michelle Obama’s Passport leaked by Hacker
- Everyone should cover up their Laptop Webcams Right Now, says FBI director
- Microsoft release 7 Critical Patches for Windows, Edge, IE, Office, Flash Player & Exchange
- Adobe patches flaw in ColdFusion that opens Apps up to Attack
- Cisco Advisory - Information Disclosure Vulnerability in Multiple Cisco Products
Awareness, Education and Intelligence
- Examining the SWIFT Bank Hack: An In-depth look at the $81 Million Cyber Attack
- Locky Developers Upgrade Ransomware's Ability to perform Offline Encryption
Reports
28 September 2016
Cyber Security Incident Management, Response and Recovery Guidance
Yesterday I spoke at the R3 Summit (Resilience, Response and Recovery) in London, on the topic of Cyber Security Incident Management and response. Given the Q & A and the ensuing discussion after my talk, the attendees were particularly interested in my views on incident containment ahead of recovery. Below is a summary of what I said.
Step 1: Incident Management Planning and Preparation
The most crucial part of incident management is the preparation, it is important to always consider cyber security incidents as a ‘When’ not an ‘If’ as you plan ahead. So here’s my ‘brain dump’ of an incident management planning strategy:
Upon initially identifying a cyber security incident, the very first question to answer is; what is the actual or potential business impact of the incident? On the face of it this can be a difficult question to answer, as the facts tend to be rather scant upon initial incident identification. However, the worse case scenario, the potential business impact, must be regarded as the actual business impact until facts are presented, through incident investigation, to prove otherwise. For example, take an online database holding 10,000 user accounts, in the space of a few hours, 20 users report via the company helpdesk that their accounts have been hacked into. Without further facts it should be assumed the entire database, all 10,000 user accounts, are compromised. This should remain the case until further facts are established to disprove which accounts have been and not been compromised. Cyber security incident investigations can take weeks to complete, and may never reach a conclusive finding on the scope of IT system or data compromise, in which case the worst case scenario must remain adopted.
Step 3: Incident Containment
Once the actual or potential business impact is understood, the next thought should be to contain the incident. The objective of containment is to limit the business impact of an incident. This is where the preparation work and the identification stage in knowing the business impact comes into play, if the potential cost and reputational damage caused by an incident, is greater than taking down business services over a period of time, then the correct business decision is to pull the plug on the service. So incident recovery may have to take a back seat for a while in order to protect the business’s overall interests. If this means pulling a plug on a busy ecommerce website, or downing an entire company network, if this course of action is the lesser of the two evils in terms of business impact, it is always the correct decision to take. Judging the business impact in knowing how long business systems need to remain down depends on Step 4.
Step 4: Incident Investigation and Forensics
As most cyber security incidents involve law breaking, whether external hackers or internal disgruntled staff, your servers and infrastructure must to be regarded as a crime scene, and so processed accordingly. There is always forensic data to collect, which may hold vital clues to the incident cause and scope, often these data clues are volatile, and can be lost if not collected quickly and correctly. Therefore any investigation and forensics work must be performed by an appropriate qualified internal or third party, while ensuring there is a legal ‘chain of custody’, in case either criminal or civil action occurs down the line. The amount of time to engage and complete computer forensic investigations can be significantly reduced, if you plan for them as part of the incident management preparation (step 1). If you do not have any qualified resource within your organisation, I recommend arranging to have a third party provided external computer forensic investigator on a retainer; typically they will provide a 4 hour call out response time.
Aside from the potential court room battles, the other primary reason to perform a proper forensic investigation is to establish the facts of an incident occurred. Without knowing the detailed facts of just how the breach occurred, you cannot know whether restored systems (step 5) will be still vulnerable or not. For example if you intend to restore systems from a backup, how do you know which backup is compromised or still vulnerable? It is imperative you know exactly when and how a cyber security incident occurred before engaging a recovery process, as in repeating an incident. there can be significant business impact, especially reputationally.
Step 5: Incident Recovery
Only once the facts of the incident are fully known, can you ensure eradication of the incident vulnerabilities and/or malware, and confidently recover systems and business services.
Step 6: Learning the Lessons
The final stage of cyber security incident management, and arguably the second most important step after the incident management preparation, is ensuring the business learns lessons from incidents. This is a healthy way to improve the business security posture, and there is nothing worse than repeating an incident.
The most crucial part of incident management is the preparation, it is important to always consider cyber security incidents as a ‘When’ not an ‘If’ as you plan ahead. So here’s my ‘brain dump’ of an incident management planning strategy:
- A company Cyber Security Incident Management Policy
- It must define what the company (aka the board) consider as a cyber security incident
- Cyber Security Incident notification communications channel or even better a reporting application/system
- Upon identifying an incident who do staff notify (the incident management team)
- Staff awareness of how to detect and report incidents is a key element.
- Verify the ability to detect incidents, not just IT system alerts, but human side (staff)
- Document the Incident Management Team and Response Plan
- Incident Management Team
- A pool of contacts with responsibility or expertise covering every possible type and aspect of a cyber security incident
- An Incident Management Team will be assembled based on what’s required for specific cyber security incident types
- Note. Every team member must play an active part or not be in the team
- Communication plan i.e. document team member phone numbers and a have dedicated incident management telephone conference call line
- Do not rely on computer IT systems like email (what if they are taken down)
- Tools (forensics) and an ability to IT access systems and logs (to investigate and obtain incident facts)
- Business Risk Assessment
- The business critical services must be risk assessed, so the business impact of any incident can be known and understood by the incident management team
- Cyber Threat Assessment
- Performing a cyber threat assessment against critical business services, aside from possible risk mitigation, threat assessing enables various cyber attack scenarios to be documented and incident response planned for and tested. Threat assessments can play a key role in helping the cyber security incident management teams prepare for incidents.
- Test the Cyber Security Incident Management Plan regularly. (at the very least annually)
- Use different attack / breach scenarios
- Always keep Incident Management Team documentation up to date (at least a quarterly review of documentation)
Upon initially identifying a cyber security incident, the very first question to answer is; what is the actual or potential business impact of the incident? On the face of it this can be a difficult question to answer, as the facts tend to be rather scant upon initial incident identification. However, the worse case scenario, the potential business impact, must be regarded as the actual business impact until facts are presented, through incident investigation, to prove otherwise. For example, take an online database holding 10,000 user accounts, in the space of a few hours, 20 users report via the company helpdesk that their accounts have been hacked into. Without further facts it should be assumed the entire database, all 10,000 user accounts, are compromised. This should remain the case until further facts are established to disprove which accounts have been and not been compromised. Cyber security incident investigations can take weeks to complete, and may never reach a conclusive finding on the scope of IT system or data compromise, in which case the worst case scenario must remain adopted.
Step 3: Incident Containment
Once the actual or potential business impact is understood, the next thought should be to contain the incident. The objective of containment is to limit the business impact of an incident. This is where the preparation work and the identification stage in knowing the business impact comes into play, if the potential cost and reputational damage caused by an incident, is greater than taking down business services over a period of time, then the correct business decision is to pull the plug on the service. So incident recovery may have to take a back seat for a while in order to protect the business’s overall interests. If this means pulling a plug on a busy ecommerce website, or downing an entire company network, if this course of action is the lesser of the two evils in terms of business impact, it is always the correct decision to take. Judging the business impact in knowing how long business systems need to remain down depends on Step 4.
Step 4: Incident Investigation and Forensics
As most cyber security incidents involve law breaking, whether external hackers or internal disgruntled staff, your servers and infrastructure must to be regarded as a crime scene, and so processed accordingly. There is always forensic data to collect, which may hold vital clues to the incident cause and scope, often these data clues are volatile, and can be lost if not collected quickly and correctly. Therefore any investigation and forensics work must be performed by an appropriate qualified internal or third party, while ensuring there is a legal ‘chain of custody’, in case either criminal or civil action occurs down the line. The amount of time to engage and complete computer forensic investigations can be significantly reduced, if you plan for them as part of the incident management preparation (step 1). If you do not have any qualified resource within your organisation, I recommend arranging to have a third party provided external computer forensic investigator on a retainer; typically they will provide a 4 hour call out response time.
Aside from the potential court room battles, the other primary reason to perform a proper forensic investigation is to establish the facts of an incident occurred. Without knowing the detailed facts of just how the breach occurred, you cannot know whether restored systems (step 5) will be still vulnerable or not. For example if you intend to restore systems from a backup, how do you know which backup is compromised or still vulnerable? It is imperative you know exactly when and how a cyber security incident occurred before engaging a recovery process, as in repeating an incident. there can be significant business impact, especially reputationally.
Step 5: Incident Recovery
Only once the facts of the incident are fully known, can you ensure eradication of the incident vulnerabilities and/or malware, and confidently recover systems and business services.
Step 6: Learning the Lessons
The final stage of cyber security incident management, and arguably the second most important step after the incident management preparation, is ensuring the business learns lessons from incidents. This is a healthy way to improve the business security posture, and there is nothing worse than repeating an incident.
23 September 2016
Yahoo's Mindblowing One Billion User Account Data Breach: Industry Analysis
Today I received several interesting cyber security expert views on the Yahoo breach following my blog post yesterday - Yahoo, The Largest Data Breach in History...so far,
Broken Security Model?
Paul German, VP EMEA at Certes, a specialist in cyber security and encryption, believes the Yahoo hackers were able to steal such vast amounts of account data due to a problem with the cyber security model of 'Protect, Detect and React'. Specifically the time in detecting the protection had been overcome. In Yahoo's case this time lag appears to be months and possibly even years, which allowed the hackers plenty of time to scout around the inside network undetected and extract such huge amounts of data out. To counter this lag, Paul suggests any potential hacker access to the data should be contained, I'm guessing by cranking down on data access control. Here's his full comments below.
“The problem lies in the face that once hackers cross a company’s carefully laid out cyber defences, the network, and the treasure trove of data within it, is their oyster. Moving laterally, they are able to siphon off huge swathes of valuable information difficulty until they are detected, often months after the initial breach.
“The problem lies in the current cyber security model which takes a, ‘protect’, ‘detect’, ‘react’ approach. There is a significant lag between the protection being sidestepped and the criminal being detected. Currently this leaves a hacker free rummage through a company’s most sensitive data, wreaking havoc. There is a fundamental step missing – at whatever point a hacker enters a network they must be contained, restricting the data they can access and the damage they can inflict before they are detected.
“Most businesses now see a security breach as a ‘when’ rather than an ‘if’ situation, and it is vital that they take steps limit the damage and protect the data of thousands, if not millions of consumers.” Paul German, VP EMEA at Certes.
I think Paul raises a fair point on breach containment, but that is easier said than done in reality, as information is typically a lifeblood of business services, so needs flow and be accessible by the business systems and customers, so can be difficult to restrict within its trusted zone. I do agree Paul's view that a security breach should be regarded as a 'when' not an 'if', business should have a proven incident management plan which reflects that.
In better detecting security breaches, businesses should invest more in a combination of technology, business management processes (i.e. risk & cyber threat assessments) and staff awareness to improve breach detection capabilities. In addition investing in an external cyber threat intelligence service adds another string to the data breach detect bow, with such services able to spot when cyber criminals peddle stolen company data on the dark web. Remember it is believed Yahoo first learnt of their data breach following reports of a hacker trying to sell 200M Yahoo accounts on the dark web, which is said to have sparked their investigations.
Jamie Graves Ph.D, co- founder and CEO of Cyber Security company, ZoneFox.com, focused on the sophistication of the attack, given Yahoo's claim that it was compromised by a nation state.
A National State Attack?
“Yahoo claims that it was compromised be a nation state, which means that a hacking team with the resources of a government had penetrated their defences. This type of attack is often difficult to defend against, and a number of other well defended organisations have fallen victim to this type of attack."
“Although the size of the breach is staggering, what has stunned the industry most is the fact that it has taken Yahoo 2 years to disclose. In this time, a great deal of additional harm will have occurred to the comprised accounts ranging from account hijacking through to identity theft and fraud.
“The Yahoo attack highlights the reason why good detection capabilities, aligned with laws that force this form of disclosure in a short period, such as the GDPR, are crucial to help protect personal information. Furthermore, organisations must not only have rigorous Cyber Security measures in place but also a disaster recovery plan to respond immediately to a breach if the, sometimes, inevitable occurs.” Jamie Graves Ph.D, co- founder and CEO of Cyber Security company, ZoneFox.com.
I am yet to be convinced this data theft was conducted by a nation state, and here's why. Nation state email account attacks tend to be targetted to email accounts, not entire email accounts on mass, and the fact that a large chunk of the Yahoo stolen email account data was attempted to be sold on the dark web doesn't fit the nation state MO either, but hacker(s) trying to monetise from the attack.
There have been countless occasions where companies blamed data breaches on highly cyber sophisticated attacks by teams of super hackers, for it to be later confirmed as being conducted by a schoolkid script kiddie taking advantage of 12 year SQL injection vulnerability. The TalkTalk breach PR comes to mind in this regard. I have no reason to think Yahoo's security posture is poor, but without them explaining the attack methodology and presenting evidence to back up their nation-state attack claim, and there should always be evidence if they are decent at security, I will remain highly sceptical of the nation state claim.
Yahoo, The Biggest Cyber Data Theft in History...so far
Yahoo have just disclosed over 500 million of its user accounts have been compromised, that's a huge number, think about it for second, that's half a billion people across the globe affected and at risk. This is largest known data breach in history to date. We know the Yahoo account data were stolen in late 2014, said the hack is said to have been orchestrated by state-sponsored actors, although there's no evidence to back this claim up.
Yahoo has not disclosed how the data was hacked, or why it has taken almost two years to either discover the breach or disclosure the breach publically. A cynic might say Yahoo delayed informing its massive user base until after it's recent £3.7 billion sale to Verizon was done and dusted. However in late July 2016 hackers were found offering 200 million Yahoo accounts for sale on the dark web (www.telegraph.co.uk/200-million-yahoo-account-details-for-sale-online), so it is likely the 2014 data theft was discovered on the back of investigating that.
The stolen Yahoo account data included names, email addresses, telephone numbers, dates of birth, and security questions and answers. Surprisingly a chunk of the security questions and answers were not encrypted by Yahoo. I always recommend companies treat the protection of account security questions and answers at the same degree as account passwords, given they can be typically used just like a password access an account via a password reset function, including accounts used with other websites. This is especially important on email accounts, as often that is where the password reset links are sent as part of the password reset process.
Advice 1: Reset Your Yahoo Password
Yahoo stated account passwords were stored as a hashed value using bcrypt. That's good practice, especially in using bcrypt. However my advice is to play it safe and reset the password, it's good practice to change your password regularly anyway. And if you use that same password on any other websites, change it there too.
Advice 2: Change Your Security Questions and Answers
Yahoo users should change their security question and answers, click here to do this on the Yahoo website. If users use the same Yahoo security questions and answers on other accounts, they also need to be changed, especially where they can be used to reset passwords and/or gain access to the account. Sure this will be a difficult task to check and complete, but Yahoo users should assume their Yahoo 'security questions and answers' together with their name, email address and date of birth, are known by cyber criminals.
Advice 3: Be Extra Vigilant
Yahoo users should be extra vigilant for phishing scam emails, which may be crafted using the stolen Yahoo personal information to look highly authentic. Also check for any suspicious activity in the email account, especially any signs that someone else has been using it.
04 September 2016
Cyber Security Roundup for August 2016
The fallout from massive data breaches in recent years continued to dominate the August headlines. Dropbox enforced password changes for 68 million users after accounts as a result of the 2012 Dropbox breach, when a Dropbox employee stole a load of account details. Meanwhile over 200 million Yahoo user credentials were found up for sale on the dark web. The large user account data breaches didn’t stop there; several large online user forums operating on vBulletin were found to be vulnerable and compromised with SQL injection attacks, leading to the theft of millions of forum user account details.
Ransomware continues to plague all industries, especially the UK health sector, with half of all NHS Trusts confirming ransomware infiltrations. The Locky ransomware continues to be updated by cybercriminals, making the malware much harder for anti-virus software to detect and prevent.
Finally a report by ‘Cybersecurity Ventures’ predicts a Cyber-Apocalypse, estimating that cybercrime will cost the world in excess of £4.5 trillion annually by 2021.
News
Ransomware continues to plague all industries, especially the UK health sector, with half of all NHS Trusts confirming ransomware infiltrations. The Locky ransomware continues to be updated by cybercriminals, making the malware much harder for anti-virus software to detect and prevent.
Finally a report by ‘Cybersecurity Ventures’ predicts a Cyber-Apocalypse, estimating that cybercrime will cost the world in excess of £4.5 trillion annually by 2021.
News
- Dropbox Hack 'affected 68 million users'
- 200 Million Yahoo user credentials for sale on Dark Web
- Hackers have Stolen £49 million worth of Bitcoins
- Epic Games Forums Hacked with SQL Injection, over 800,000 User Credentials Stolen
- Opera (web browser) resets Passwords after sync server Hacked
- Telegram API flaw leaks 15 Million Iranian users' Data
- 123-Reg Suffers Major DDoS Attack
- Swift warns banks of more Cyber-Thefts
- Tech-savvy targeted by ID thieves, says Experian
- Advanced Malware linked to South China Sea Cyber-Attacks
- Hackers exploit vBulletin SQL Flaws to access 27M accounts on 11 Websites
- 47% of NHS Trusts in England admit to falling victim to Ransomware
- Jimmy Wales suffers Twitter Account Hacked
- Microsoft release 5 Critical Patches for Windows, Edge, IE, Office & PDF Library
- Adobe issued Hotfix for Critical Information Disclosure Vulnerability in ColdFusion
- Apple Rushes Out iOS Software Update To Fix Spyware Threat
- Cisco Advisory “We have started publishing fixes” for NSA-linked Exploits
- Locky Ransomware Spread in Global Campaign against Health Sector
- Latest Locky version on the Loose
- Researcher warns of Cyber-Threat to Mergers and Acquisitions
- CyberSecurity Market Report: Cybercrime cost excess of £4.5 trillion annually by 2021
- Imperva Annual DDoS Threat Landscape Report: UK 'too attractive' to DDoS Attackers
01 August 2016
Cyber Security Roundup for July 2016
In July there were several reports affirming the continued escalation of Cybecrime in the UK, with the National Crime Agency (NCA) including cybercrime in its crime statistics for the first time, confirming there were more incidents of cybercrime than physical crime in the UK. NCA concluded that UK businesses and law enforcement were losing a “cyber arms race” with online criminals. The Information Commission’s Office (ICO) highlighted the UK Health and Local Government as the worse industries for data protection, accounting for 41% of data breaches reported to the ICO in Q1 of this year.
The EU approved “EU-US Privacy Shield” as a replacement for ‘Safe Harbor’, however there is speculation this is merely a temporary fix, as the EU data protection committee, Working Party 29, raised concerns with the Privacy Shield agreement, which they intend to address in 2017.
BT's broadband outages in July has led to concern about the resilience of the UK's national digital infrastructure to cyber attacks.
In the games industry Pokemon Go dominated the gaming industry and cyber security headlines, with many gamers running into personal cyber security issues in their attempts to play Pokemon Go ahead of its official UK launch in mid July. Gamers were duped into downloading malicious versions of the game, and there were reports of gamers having account credential compromises as a result of signing up with dubious game downloading websites. A hacking group also claimed to had taken down the Pokemon Go servers for several hours with a DDoS attack. In other games industry news Clash of Kings and Warframe account credentials were reported to have been compromised on mass via a support forum.
There was plenty of speculation and evidence of a 'cold war' Cyberwarfare escalation, with reports of hacks against democratic (Clinton) groups in the US presidential race, and reports of large scale and 'professional' cyber attacks hitting Russian government agencies.
The EU approved “EU-US Privacy Shield” as a replacement for ‘Safe Harbor’, however there is speculation this is merely a temporary fix, as the EU data protection committee, Working Party 29, raised concerns with the Privacy Shield agreement, which they intend to address in 2017.
BT's broadband outages in July has led to concern about the resilience of the UK's national digital infrastructure to cyber attacks.
In the games industry Pokemon Go dominated the gaming industry and cyber security headlines, with many gamers running into personal cyber security issues in their attempts to play Pokemon Go ahead of its official UK launch in mid July. Gamers were duped into downloading malicious versions of the game, and there were reports of gamers having account credential compromises as a result of signing up with dubious game downloading websites. A hacking group also claimed to had taken down the Pokemon Go servers for several hours with a DDoS attack. In other games industry news Clash of Kings and Warframe account credentials were reported to have been compromised on mass via a support forum.
There was plenty of speculation and evidence of a 'cold war' Cyberwarfare escalation, with reports of hacks against democratic (Clinton) groups in the US presidential race, and reports of large scale and 'professional' cyber attacks hitting Russian government agencies.
News
- Health Sector and Local Government Tops UK Data Breach List
- EU-US Privacy Shield data pact gets European Approval
- Cyber-Crime now Tops Traditional Crime in UK
- Criminals are winning 'Cyber Arms Race' - National Crime Agency
- 1.6m ‘Clash of Kings’ forum accounts Stolen
- Over 750,000 Warframe Accounts Compromised
- O2 Customers' details sold on the Dark Web
- Second BT Outage calls into Question the Security of Critical Infrastructure
- Pokemon Go DDoS Attack Claimed by the PoodleCorp Hacking Group
- Four Cyber Attacks On UK Railways In A Year
- Wireless Keyboards 'easy' to Snoop on
- iTunes Users Targeted In Email Phishing Scam
- Rival Cyber-Gang leaks private keys of Chimera Ransomware
- Russia Cyber Attack: Large hack 'Hits Government'
- Check Point tracks two waves of Cerber Ransomware hitting US, UK
- Apple Patches Remote Code Execution Flaws
- Symantec Security Software had 'Critical' Flaws
- Microsoft release 6 Critical Patches for Windows, Edge, IE, Office & Adobe Flash Player


