Your go-to blog for the latest UK Cybersecurity News, Trends, and Developments. Covering Hacking, Data Breaches, Privacy, and Security Standards.
Thursday, 16 March 2017
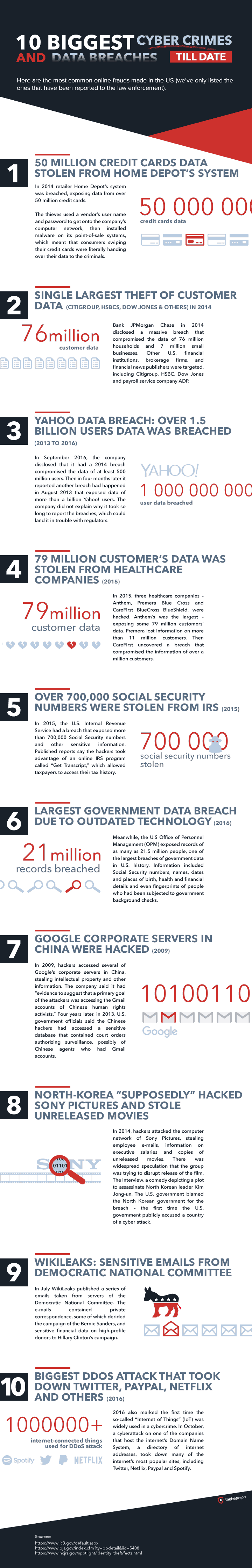
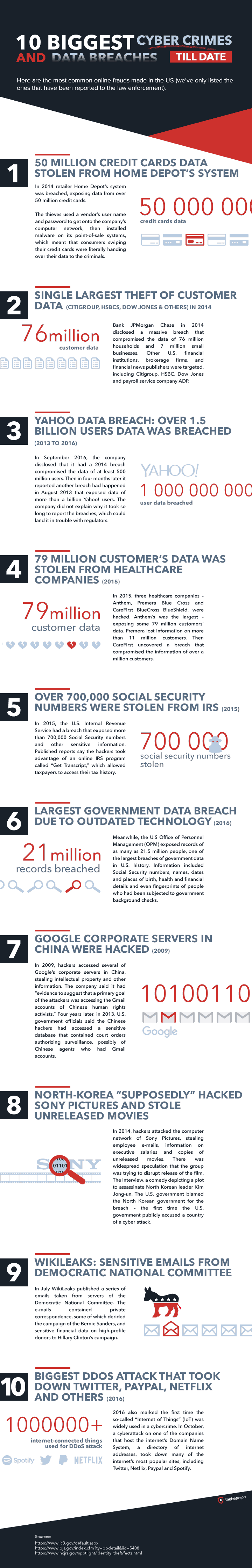
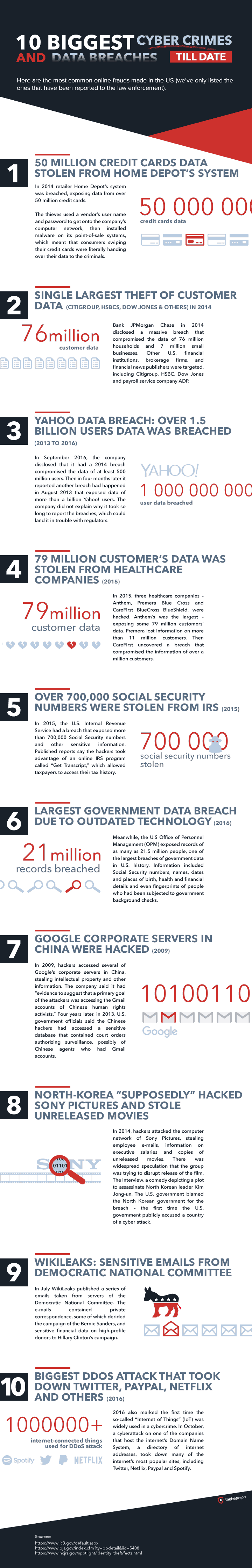
10 Biggest Cyber Crimes and Data Breaches...so far
The good folk at The Best VPN have put together an Infographic summarising ten of the worst "known" cyber attacks and data breaches to date, its a good recap of the high stakes when cyber security goes wrong.
Thursday, 9 March 2017
PCI DSS Penalties & Fines? Cyber Insurance? How to Estimate the Cost of a Payment Card Breach
How much does a payment card breach cost? How large are the potential fines? What happens if we aren't PCI DSS compliant and suffer a cardholder breach?
Those are common unanswered questions which businesses accepting and processing debit and credit card payments rise, businesses which are required to be compliant with the Payment Card Industry Data Security Standard (PCI DSS). In recent years a growing number of UK businesses are taking out cybersecurity insurance, and are more pressingly wanting to know whether their insurance coverage is sufficient enough to cover the cost of a payment card data breach.
Those are common unanswered questions which businesses accepting and processing debit and credit card payments rise, businesses which are required to be compliant with the Payment Card Industry Data Security Standard (PCI DSS). In recent years a growing number of UK businesses are taking out cybersecurity insurance, and are more pressingly wanting to know whether their insurance coverage is sufficient enough to cover the cost of a payment card data breach.
It is not possible to produce a formula or calculator to provide precise payment card breach costs on a per card compromised basis, as no two business payment operations are ever the same, and there are just too many factors that can impact the overall cost of a breach. So instead I have put together the following six pointers to aid the estimation of a payment card breach.
Calculating the Approximate cost of a Payment Card Breach
1. All Payment Card Data breaches must be investigated by PCI qualified Forensic Investigator (PFI). Depending on the technical complexity and scale of the breach, the cost equates to the number of investigator hours and days required, depending that expect to fork out around £20,000 to £100,000 for a PFI. It is worth noting should a business not play ball with the acquiring bank, card brands and card issuers in appointing a PFI, they can remove entire business' capability to take card payments altogether, so there is no choice but to dig deep from the outset upon a data breach discovery.
2. Following the forensic investigation, completion of remediation work and a successful PCI DSS level 1 QSA assessment is required. Remediation work and Qualified Security Assessor (QSA) assessment as a PCI DSS level 1 merchant or processor typically costs up to £100,000, depending on the environment that is in-scope of compliance. This will be a considerable new overhead for environments deemed as PCI DSS level 2, 3 or 4, as these would have previously been self-assessed by the business.
3. The cost per payment card breach is very subjective, however, Verizon's 2015 Data Breach Investigations Report page 30 figure 23, gives a good indication of the "cost per card lost", which I have converted from US dollars.
Optimists should read the left side of the table, pessimists should read the right side of the table.
4. Often there will be a penalty surcharge levied per transaction following a breach, adding an increase to every payment transaction.
5. Reputational damages, loss of customer and client trust in the business and brand, this is a hard figure to quantify, but it is worth noting most cyber insurance policies do not cover any business losses due to reputational damages following data breaches.
6. The Information Commissioners Office (ICO) regards payment card data as Personal Information, which means they can add an up to £500,000 per payment card data breaches. For example in 2015, the ICO fined insurance firm Staysure £175,000 after 5,000 hacked card details used for fraud.
And from May 2018 when the new GDPR data privacy regulation kicks in, potential data protection fines will ramp significantly, especially for large enterprises, with fines of up to 4% of the global turnover of the entire business.
And from May 2018 when the new GDPR data privacy regulation kicks in, potential data protection fines will ramp significantly, especially for large enterprises, with fines of up to 4% of the global turnover of the entire business.
So take the worse case breach scenario, namely a compromise of all payment cards ever stored and processed, apply the above costs, and you should have a worse case scenario ballpark figure. If that number doesn't focus minds and incentivise a robust PCI DSS compliance programme and investment in cyber security, nothing will.
Why Passing a PCI DSS Assesment isn't a 'Get out of Jail Free Card'
No business operating in a PCI DSS compliant state is known to have been breached. Passing a PCI DSS assessment does not mean the business is actually PCI DSS compliant, and it certainly is not a 'get out of jail free' card or carries any weight if a breach occurs. A PCI DSS compliance business means the in-scope of compliance environment and operations meets every single PCI DSS requirement in a continual state of operation, 365 days a year, 24 hours a day, and for every single second.
Wednesday, 1 March 2017
Cyber Security Roundup for February 2017
Printing outs sent Printers open on the Internet
Third party cloud security comes into question after CloudFlare, a popular content delivery network used by more than 5.5 million sites, accidentally leaked customers' sensitive information for months. If you are a CloudFlare customer I strongly advise to change your passwords. The Yahoo’s sale to Verizon has dropped by $350m following Yahoo’s recently reported data breaches. And Sports Direct came in for criticism for not advising its 30,000 staff that their personal details had been hacked.
Back on the technical security front, Google researchers illustrated security weakness in SHA-1. The cryptographic hashing algorithm has not been considered secure since 2010, so the research is a poignant reminder to never use SHA-1 on new configurations, and to review and phase all SHA-1 usage in any existing solutions, such as site-to-site VPNs and within application development, go for SHA-256 or SHA-3 hashing instead.
Back on the technical security front, Google researchers illustrated security weakness in SHA-1. The cryptographic hashing algorithm has not been considered secure since 2010, so the research is a poignant reminder to never use SHA-1 on new configurations, and to review and phase all SHA-1 usage in any existing solutions, such as site-to-site VPNs and within application development, go for SHA-256 or SHA-3 hashing instead.
News
- Major CloudFlare Bug Leaked Sensitive Data from Customers’ Websites
- Verizon Yahoo Deal at Lower Price after Hacks
- Sports Direct 'hid data breach from Staff'
- Google Research Cracks SHA-1 (Cryptographic Hashing Algorithm)
- 40,000 WordPress blogs defaced in Hack Attacks
- Hack of Aberdeen City Council website cost the local authority £10,000
- London Hospital fined £200,000 over fertility Data Breach
- Script-Kiddie Hacker Hijacks Printers through insecure Firewalls
- UK firms 'chronically understaffed' in face of Cyber Threat
- Microsoft release 1 Critical Patch for Adobe Flash Player
- Google reveals bug prior to Microsoft patch
- Only 1.2% of Android devices use latest OS
Friday, 24 February 2017
Blueprint for Secure Driverless Cars
Robust Cyber Security is an intrinsic requirement with all connected technology in our daily lives, and it is especially challenging with new cutting edge technological advances. Connected and driverless cars promises to be one greatest technological advances of the century, as such fascinates and excites yet at the time there are concerns. Getting cyber security right from the outset will be critical to the success of this industry, as vulnerable connected computer controlled cars is a matter of life and death. Securing the ever increasing sophistication and complexity of computers that control cars is certainly not for the faint hearted.
The car industry recognises trust and security go hand in hand, so in league with the likes of Aeris, Intel and Uber, the industry formed an industry wide organisation called FASTR - Future of Automotive Security Technology Research. FASTR seeks to enable automotive security by driving cybersecurity across the entire vehicle manufacturing supply chain, to ensure smart cars will be secure from cyber attack.
FASTR recently produced an interesting infographic covering their approach to cyber security, it also has great stats about the car's of today and the cars of tomorrow. If you are interested in learning more about FASTR's approach, check out their Manufesto

The car industry recognises trust and security go hand in hand, so in league with the likes of Aeris, Intel and Uber, the industry formed an industry wide organisation called FASTR - Future of Automotive Security Technology Research. FASTR seeks to enable automotive security by driving cybersecurity across the entire vehicle manufacturing supply chain, to ensure smart cars will be secure from cyber attack.
FASTR recently produced an interesting infographic covering their approach to cyber security, it also has great stats about the car's of today and the cars of tomorrow. If you are interested in learning more about FASTR's approach, check out their Manufesto
Tuesday, 21 February 2017
Google & Bing UK Piracy Website Blocking is a Bad Idea for Security
Search engine giants Google and Bing have announced an agreement to make it harder for UK internet users to find pirated films, music and illegally stream football by blocking websites. It appears they have bowed to pressure by the entertainments industry and the UK government's Department for Culture, Media and Sport, to sign up to a voluntary code of practice.
I certainly don’t condone piracy or digital theft of any kind, but blocking websites is really a terrible idea for the security, privacy and even piracy prevention and enforcement, as it will just drive more people onto the dark web looking for the material they desire. I fear this will only serve to pour petrol on the illicit activities of the dark web by the swelling dark web ‘punters’. What's worst is new and inexperienced UK dark web users are vastly more likely to end up as victims of cyber crime in their desperate attempts to find banned content.
This is a 'sweeping under the carpet' approach, driving piracy underground onto the dark web where it will be almost impossible to police and prevent. A much more sensible approach to better educate the masses about morality and impact of digital theft. If the UK government are serious about protecting our digital economy from digital piracy, then this morality education needs to start within UK schools.
I am sure privacy advocates will be looking for their Guy Fawkes masks alarmed that the UK government are seemingly involved in pushing the UK's two major search engines into blocking Internet content to UK citizens.
Lee Munson, a security researcher at Comparitech.com, said.
“The new voluntary code of practice pledged by major search engines is bad news for anyone looking to download or consume content without paying for it but good news for everyone who wants to stay safe online.
While not every pirate site hosts or links to misnamed files, Trojan-laden porn or malware-infected movie files, many do and, even though security software should be in place, we all know that a great many people do run into trouble on these sorts of sites.
That’s not to say that this new initiative will make malicious files a thing of the past though – the determined will still find the websites they need, however far down the search engine results pages they may fall, and the sharing of such files between family and friends will no doubt carry on unabated.”
That’s not to say that this new initiative will make malicious files a thing of the past though – the determined will still find the websites they need, however far down the search engine results pages they may fall, and the sharing of such files between family and friends will no doubt carry on unabated.”
Tuesday, 31 January 2017
Cyber Security Roundup for January 2017
Lloyds Banking Services were hit by a massive 3-day long DDoS attack in mid-January, impacting millions of Lloyds, Halifax and Bank of Scotland customer’s ability to conduct online and mobile banking. Lloyds weren't the only UK business hit with a major DDoS attack in January, web hosting firm 123-Reg was taken down by another large DDoS attack. It seems major DDoS attacks are set to continue in 2017, their scale and capability fuelled by the rise of insecure IoT devices popping online. I think large scale DDoS attacks will be a major menace to the UK national and financial infrastructure for the years to come.
For the first time 'Cyber Crime' statistics were included in the England and Wales crime survey, with over 3.6 million fraud cases and over 2 million computer misused offences recorded in 2016, which is more than the typical 'physical world' recorded crime. It is worth considering that not all cybercrime is reported in England and Wales, in my view the majority of UK cybercrime isn't reported.
The latest Beazley Breach Insights Report predicts the number of Ransomware attacks will double again in 2017, and UK schools are the latest sector to become victims of Ransomware. With the growing ransomware threat in mind, the Malware Hunters Team produce an interesting breakdown of a new ransomware strain called FireCrypt this month, well worth a look if you are interested in how the bad guys create, evolve and use ransomware tools.
There are lessons for the UK call centre industry to learn from a US telemarketing firm, which had a database of 400,000 call recordings reportedly breached. These voice recordings were said to hold personal information and more concerningly debit/credit card information. This breach is a reminder of the importance of adequately securing call recording data with call centres, and of the Payment Card Industry Data Security Standard (PCI DSS) industry regulation requirement 3.2, which states debit/credit card “3 or 4 digit security codes”, known in the industry as Sensitive Authentication Data, is never permitted to be recorded or stored beyond the authorisation of the card payment transaction. This is a PCI DSS requirement that far too many UK call centre businesses turn a blind eye to. This strict requirement is there for a reason, as if fraudsters get hold of credit/debit card data with the 3/4 digit security code, they can instantly commit fraud without having possession of the customer's payment card.
- Lloyds Online Banking Services taken down by Huge 3 day DDoS Attack
- Yahoo sale delayed following Security Breaches
- 3.6 Million Fraud Cases & 2 Million Computer Misuse offences a year - UK Crime Survey
- UK’s Largest Hosting Firm 123-Reg hit by DDoS Attack
- Fraudsters demand £8000 from UK Schools to Unlock Encrypted Data
- Royal & Sun Alliance fined £150K after Hard Drive Loss
- US Telemarketing Firm Leaks 400K Call Recordings, some containing Payment Data
- Thousands Warned they may be Victims of Rogue Webmaster
- Phone-Cracking Firm Cellebrite Hacked
- Microsoft release 1 Critical Patch for Adobe Flash Player
- WordPress updated to fend off SQL and XSS bugs
- Mozilla issues five critical patches for Firefox and Firefox ESR
- Overview of the new FireCrypt Ransomware
- Zeus malware resurfaces as Zbot/Terdot, integrates legitimate apps
Reports
Thursday, 5 January 2017
Cyber Security Roundup 2016: The Year of the Big Data Hack
A decade ago I was walking into Boardrooms clutching newspaper clippings of half dozen data breaches which had occurred during the previous years, in a bid to warn of future threats and to persuade executives to increase their information security budgets. Those days are long gone, as most executives I encounter tend to be already worried about the cyber threat to their business, all reinforced by the mainstream media which today reports hacks most days.
"Big Data" is a recent marketing buzzword used to usher in the age of businesses utilising the vasts amount of data which they process and store for increasing efficiently and profit. The problem is much of this "Big Data" is our personal data, and there are cyber criminals also seeking to profit from it. So here we are in the era of "Big Data Hacks", which sums up 2016 quite well.
I have compiled a list of media headlines of data breaches in 2016 below, the volumes involved with these data theft hacks are truly mind–boggling. Yahoo on their own had 1.5 billion personal records stolen in two cyber attacks. It isn't necessary that stealing digital text data in such volumes is difficult, but have to wonder about what level of IT security was in place to protect such large volumes of personal data in the first place.
DDoS attacks continued to grow in strength in 2016, thanks to the explosion of the Internet of Things, with hackers creating huge DDoS botnets from insecure and rushed IoT devices, which frankly have no business of being sold and placed online with default passwords and basic software vulnerabilities.
2016 was also the year Ransomware made a huge comeback. The UK public sector seems particularly vulnerable to ransomware infections, with cyber criminals making millions by evolving various strains of ransomware and catching victims out with the age old infection techniques of phishing emails, malware infected websites and trojan software.
In 2017 we can expect to see more Big Data hacks and huge IoT fuelled DDoS attacks. Ransomware isn't going to go away either, however I am most concerned we'll see our first IoT attack which results in physical world damage and human harm in 2017.
Personal Data Theft and Data Breaches in 2016
"Big Data" is a recent marketing buzzword used to usher in the age of businesses utilising the vasts amount of data which they process and store for increasing efficiently and profit. The problem is much of this "Big Data" is our personal data, and there are cyber criminals also seeking to profit from it. So here we are in the era of "Big Data Hacks", which sums up 2016 quite well.
I have compiled a list of media headlines of data breaches in 2016 below, the volumes involved with these data theft hacks are truly mind–boggling. Yahoo on their own had 1.5 billion personal records stolen in two cyber attacks. It isn't necessary that stealing digital text data in such volumes is difficult, but have to wonder about what level of IT security was in place to protect such large volumes of personal data in the first place.
DDoS attacks continued to grow in strength in 2016, thanks to the explosion of the Internet of Things, with hackers creating huge DDoS botnets from insecure and rushed IoT devices, which frankly have no business of being sold and placed online with default passwords and basic software vulnerabilities.
2016 was also the year Ransomware made a huge comeback. The UK public sector seems particularly vulnerable to ransomware infections, with cyber criminals making millions by evolving various strains of ransomware and catching victims out with the age old infection techniques of phishing emails, malware infected websites and trojan software.
In 2017 we can expect to see more Big Data hacks and huge IoT fuelled DDoS attacks. Ransomware isn't going to go away either, however I am most concerned we'll see our first IoT attack which results in physical world damage and human harm in 2017.
Personal Data Theft and Data Breaches in 2016
- Yahoo Hack: 1 Billion User AccountsCompromised by biggest Data Breach in History
- KFC's Colonel Club Hacked, 1.2 Million advised to Change Passwords
- DailyMotion breached, 85 Million Accounts Stolen
- LinkedIn’s Lynda.com breached, 55,000 user password reset, 9.5 Million Users Warned
- Star Wars card firm Topps hit by 'unforgiveable' Hack
- Three Data Breach Cyber Hack: Six Million Customers Data at Risk
- National Lottery Hack: 26,500 Players' Online Accounts Accessed
- Capgemini Leaks 780,000 Michael Page Job Candidate CVs
- Hackers steal 43 million credentials from Weebly
- Yahoo Hit in Worst Hack Ever, Over 500 Million Accounts Stolen
- Dropbox Hack 'affected 68 Million users'
- 200 Million Yahoo user credentials for sale on Dark Web
- Tesco Bank Hack: £2.5m refunded to 20,000 Customers
- Epic Games Forums Hacked with SQL Injection, over 800,000 User Credentials Stolen
- Telegram API flaw leaks 15 Million Iranian users' Data
- Hackers exploit vBulletin SQL Flaws to access 27M accounts on 11 Websites
- 1.6m ‘Clash of Kings’ forum accounts Stolen
- Over 750,000 Warframe Accounts Compromised
- O2 Customers' details sold on the Dark Web
- 'Significant' number of TeamViewer accounts Hacked
- 32 Million Twitter Logins found up for Sale
- Welsh Police fined £150,000 by ICO after revealing Sex Offender Identities in Error
- 117 million LinkedIn Email Credentials found for Sale on the Dark Web
- Email Error Leaks Hundreds of Northern Ireland Prison Officer Details
- World-Check Terrorism Database Exposed Online
- Chelsea & Westminster Trust fined £180K after email reveals over 700 HIV Patients
- ICO Fines Blackpool NHS Trust £185,000 for leaking staff data via Excel Error
- Kent Police fined £80k for serious Domestic Abuse Data Breach
- 272 Million email Account Credentials found on the Dark Web
- MySpace and Tumblr hit by 'Mega Breach'
- National Childbirth Trust suffers major Data Breach
- Personal Details of 50 million Turkish Citizens Leaked Online
- Huge data breach leaves details of 55 million Filipino voters exposed
- 93.4 million Mexican voters exposed in massive Database
- Leak BeautifulPeople.com hack exposes data of 1.1 million users
- Cyber Criminals 'Hacked Law Firms'
Tuesday, 3 January 2017
Cyber Security Roundup for December 2016
Yahoo announced
the largest ever data breach in history, with over 1 billion Yahoo user accounts
compromised by a past cyber attack, which I covered in Yahoo's Mind-blowing One Billion Data Theft Hack. This truly humongous data hack is distinct from the
2014 breach of 500 million accounts reported by Yahoo in September. Elsewhere
KFC, Topps, The Daily Motion and LinkedIn’s Lynda.com also reported large
customer data breaches of millions of records during December.
We need to be mindful of never to "get use to" and accepting these massive numbers of hacked online accounts, by businesses we entrust with our personal information, especially where these businesses have been found 'wanting' on the cyber security defences by under investing. The old spin doctor excuses of indefensible super hacks orchestrated by sophisticated nation-state backed dark forces tends not to stand up once the facts are uncovered. There is nothing sophisticated about teenage kids using freely downloadable software to take advantage of decade old and basic security vulnerabilities.
The media and security experts continues to pour scorn on TalkTalk’s cyber security, following the firm’s poor
handling and customer advice after a cyber attack of unpatched TalkTalk
customer broadband routers.
ThyssenKrupp, a large
German steel maker firm, disclosed it was a victim of cyber intellectual
property (IP) theft. Businesses rarely admit to IP data theft given such admissions can serious harm the business's reputation and share price. Given the high media and public
attention in protecting personal data from cyber attacks, following a year of
high profile large customer record losses due to cyber attacks, it can be easy for businesses to take their eye off protecting their IP, and to become complacent with IP protection and security.
I was quoted in the Focus Training's Blog. An 'Ask the Experts' piece on 'How to Protect your business from Cyber Crime', my advice was as follows.
There was a Christmas bumper of patch releases in December, with Microsoft, VMWare, Joomla, PHP and Android all releasing patches for critical vulnerabilities.
News
- Yahoo Hack: 1 Billion User AccountsCompromised by biggest Data Breach in History
- KFC's Colonel Club Hacked, 1.2 Millionadvised to Change Passwords
- DailyMotion breached, 85 Million AccountsStolen
- TalkTalk and Post Officerouters taken offline by Cyber Attack
- TalkTalk's Wifi Hack advice is'astonishing' Customers urged to get Routers Swapped
- German Steel firm's IP stolen in Massive CyberAttack
- European Banking Breach guidelines moreStrict than EU GDPR
- Ashley Madison forced to pay £1.3m forDeceptive Security Practices
- LinkedIn’s Lynda.com breached, 55,000 userpassword reset, 9.5 Million Users Warned
- Insurers handling 'Hundreds' of Breach Claims
- Domino'sPizza advises Customers to change their Passwords
- Star Wars card firm Topps hitby 'unforgiveable' Hack
- Ask The Experts: How to Protect Your Business From Cyber Crime
- Microsoft release 6 Critical Patches for Windows, Edge, IE, Office & Adobe Flash Player
- Skype Backdoor missed by Microsoft Development Team
- Android Dirty Cow flaw is Finally Patched (CVE-2016-5195)
- Joomla flaw allows Attacker to Change passwords and Seize Websites
- 3 Critical PHP 7 Flaws Detected and Patched
- VMware fixes stored XSS vulnerability in ESXi Hypervisor
- Over 400,000 Phishing websites have been detected Each Month in 2016
- Hailstorm Methods used to spread Malware in Phishing Attacks
Labels:
Cyber Crime,
cyber security roundup,
data breach,
Data Protection,
GDPR,
hackers,
Hacking,
malware,
Microsoft,
Network Security,
password security,
Patching,
Security Awareness,
talktalk,
yahoo
Wednesday, 21 December 2016
How to Protect your Business from Cyber Crime
Today I was quoted in the Focus Training's Blog. An 'Ask the Experts' piece on 'How to Protect your business from Cyber Crime', my advice was as follows.
- Educate all business staff about dangers and latest attack methods, particularly ensuring they aware of targeted scam emails (spear phishing). Cyber criminals are increasingly targeting individual business staff members, typically those with finance responsibilities, by crafting highly convincing emails using information about the business, its staff and its suppliers. These scam emails once responded to, will typically try to convince (social engineer) individual staff members to arrange a bank transfer or payment to a bogus account operated by the cyber criminals
- Keep all Servers, PCs, Laptops, Tablets and Smart Phones operating systems and applications updated (security patching). Out of date software is vulnerable and commonly exploited by malware and hackers.
- Business staff should use unique passwords with each third party/online service used by the business. Ensuring passwords are complex and changed every 90 days. Where possible use mutli-factor authentication (I.e. password + hardware token or text message confirmation). Cyber criminals know many people use the same email and password combination across multiple websites, so when they obtain one credentials combination, usually via a third party website hack, the database of which are often dumped onto the darkweb, cyber criminals try the same stolen email and password combinations to attempt to access further online services, with the intent of stealing personal data and money.
Subscribe to:
Posts (Atom)