UK cybersecurity analysis and practitioner-led commentary on breaches, governance, regulation and provable cyber resilience.
14 September 2018
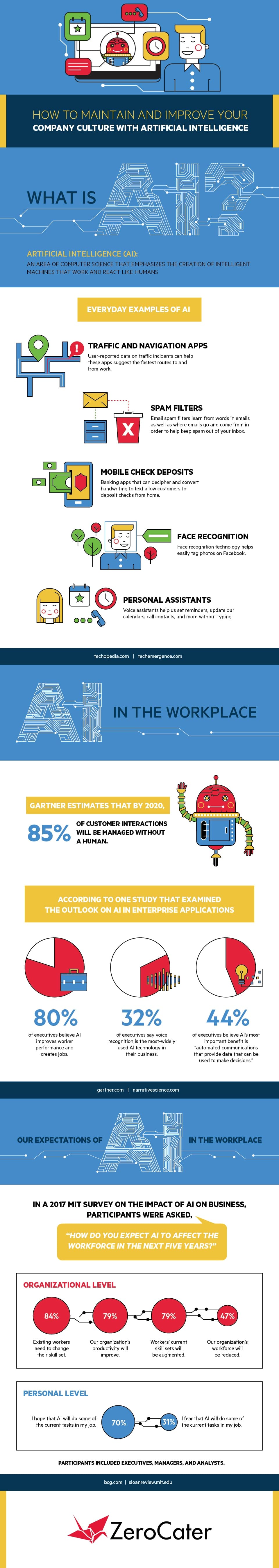
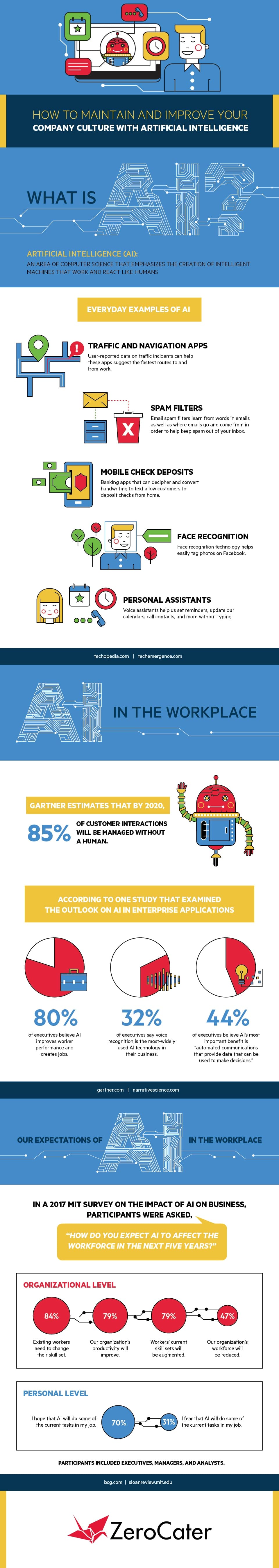
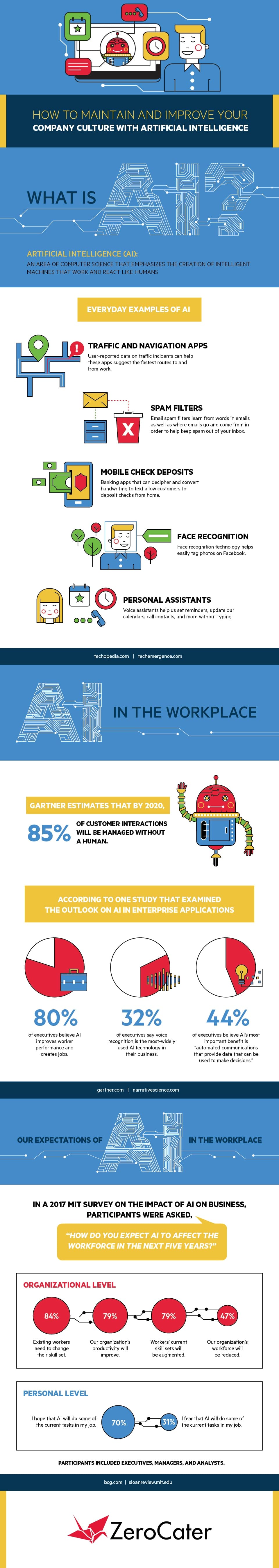
What is Artificial Intelligence (AI)?
Artificial Intelligence (AI) has many business and security benefits but has risks and concerns. AI can be a complicated subject matter to initially understand, so I thought it would be useful to share a great AI Infographic by ZeroCater, which simply explains what AI is and how it is already being adopted.
11 September 2018
British Airways Hack Update: Caused by Injected Script & PCI DSS Non-Compliance is Suspected
On Friday (7th September 2018), British Airways disclosed between 21st August 2018 and 5th September 2018, 380,000 BA customer's payment card transactions were compromised by a third party through its website and mobile app. This data included the customer's full name, email address, debit\credit card 16 digit number (PAN), expiry date and card security code i.e. CVV, CV2
Details of how the hack was orchestrated have now come to light. In a blog post RiskIQ researchers have claimed to have found evidence that a web-based card skimmer script was injected into the BA website, very similar to the approach used by the Magecard group, who are believed to be behind a similar attack against the Ticketmaster website recently. Web-based card skimmer script attacks have been occurring since 2015.
In this case, once the customer has entered their payment card details and then submits the payment either on a PC or on a touchscreen device, the malicious script executes and captures their payment card data, sending it to a virtual (VPS) server hosted in Romania. The server was hosted on a domain called baways.com and was certified (https) by Comodo to make it appear legit within the website html (code). The server domain was registered 6 days before the breach started, this obviously went undetected by BA's security, perhaps the domain registration could have been picked up by a threat intelligence service.
Other Researchers have also claimed the BA website wasn't PCI DSS compliant. Marcus Greenwood found files loaded from 7 external domains onto the BA website, and crucially said the BA payment page wasn't isolating the card payment entry within an iframe, which would prevent any third-party scripts (and XSS attacks) from being able to read the payment card form fields. The Payment Card Industry Data Security Standard (PCI DSS) is required by all organisations which accept, process, store and/or transmit debit and credit cards.
Here is the advice from CEO of global cybersecurity specialist SonicWall, Bill Conner:
"Organizations and government entities carry a responsibility to consumers and civilians alike to guard their most valuable information at all cost. While the British Airways breach may not have been as detrimental as I’m sure its culprits would have liked it to be, it should serve as a wake-up call to CTOs, CIOs and CISOs. The fact is, it is early days, and the true damage done is yet to be seen. Personal information that does not change as easily as a credit card or bank account number drive a high price on the Dark Web. This kind of Personally Identifiable Information is highly sought after by cybercriminals for monetary gain. Companies should be implementing security best practices such as a layered approach to protection, as well as proactively updating any out of date security devices, as a matter of course."
My view mass credit\debit card data (cardholder data) complete with the security code has always been targeted by cyber crooks as it is very easily sellable on the dark web, as the data only can be used in cardholder-not-present transaction fraud, where credit card holder is not physically present i.e. online, app, phone. The finger can be pointed at lack of PCI DSS compliance by merchants like BA, however, I think it is about time technology was used to improve the security of all cardholder-not-not present transactions, namely Multi-factor authentication (MFA). While MFA on all cardholder-not-present is not a silver bullet, there is no 100% security, enforced usage across all industries would certainly devalue debit\credit card data considerably.
In this case, once the customer has entered their payment card details and then submits the payment either on a PC or on a touchscreen device, the malicious script executes and captures their payment card data, sending it to a virtual (VPS) server hosted in Romania. The server was hosted on a domain called baways.com and was certified (https) by Comodo to make it appear legit within the website html (code). The server domain was registered 6 days before the breach started, this obviously went undetected by BA's security, perhaps the domain registration could have been picked up by a threat intelligence service.
Other Researchers have also claimed the BA website wasn't PCI DSS compliant. Marcus Greenwood found files loaded from 7 external domains onto the BA website, and crucially said the BA payment page wasn't isolating the card payment entry within an iframe, which would prevent any third-party scripts (and XSS attacks) from being able to read the payment card form fields. The Payment Card Industry Data Security Standard (PCI DSS) is required by all organisations which accept, process, store and/or transmit debit and credit cards.
Here is the advice from CEO of global cybersecurity specialist SonicWall, Bill Conner:
"Organizations and government entities carry a responsibility to consumers and civilians alike to guard their most valuable information at all cost. While the British Airways breach may not have been as detrimental as I’m sure its culprits would have liked it to be, it should serve as a wake-up call to CTOs, CIOs and CISOs. The fact is, it is early days, and the true damage done is yet to be seen. Personal information that does not change as easily as a credit card or bank account number drive a high price on the Dark Web. This kind of Personally Identifiable Information is highly sought after by cybercriminals for monetary gain. Companies should be implementing security best practices such as a layered approach to protection, as well as proactively updating any out of date security devices, as a matter of course."
My view mass credit\debit card data (cardholder data) complete with the security code has always been targeted by cyber crooks as it is very easily sellable on the dark web, as the data only can be used in cardholder-not-present transaction fraud, where credit card holder is not physically present i.e. online, app, phone. The finger can be pointed at lack of PCI DSS compliance by merchants like BA, however, I think it is about time technology was used to improve the security of all cardholder-not-not present transactions, namely Multi-factor authentication (MFA). While MFA on all cardholder-not-present is not a silver bullet, there is no 100% security, enforced usage across all industries would certainly devalue debit\credit card data considerably.
07 September 2018
British Airways Customer Data Stolen in Website and Mobile App Hack
In a statement, British Airways stated: "From 22:58 BST August 21 2018 until 21:45 BST September 5 2018 inclusive, the personal and financial details of customers making bookings on ba.com and the airline’s app were compromised." The airline said they will be notifying affected customers, and if anyone has been impacted to contact their bank or credit card providers.
The Telegraph reported 380,0000 payments were compromised, and that BA customers had experienced payment card fraud as a result before the BA breach disclosure, which strongly suggests unencrypted debit\credit cards were stolen.
The Telegraph reported 380,0000 payments were compromised, and that BA customers had experienced payment card fraud as a result before the BA breach disclosure, which strongly suggests unencrypted debit\credit cards were stolen.
There are no details about the data theft method at the moment, but given the statement said the BA website and BA mobile app was compromised, I think we could be looking at another example of an insecure API being exploited, as per the Air Canada breach and the T-Mobile breach last month.
We'll see what comes out in the wash over the next few days and weeks, but thanks to the GDPR, at least UK firms are quickly notifying their customers when their personal and financial data has been compromised, even if there is little detail reported about how. Without knowing how the data was compromised, customers cannot be truly assured their private data is safe. It also will be interesting to learn whether the BA systems were compliant with the Payment Card Industry Data Security Standard (PCI DSS), required by all organisations that accept, process, store and/or transmit debit and credit cards.
Update:
A spokesperson at BA said "hackers carried out a sophisticated, malicious criminal attack on its website" and impacted BA customers would be compensated.
380,000 card payment transactions were confirmed as stolen, specifically:
Update:
A spokesperson at BA said "hackers carried out a sophisticated, malicious criminal attack on its website" and impacted BA customers would be compensated.
380,000 card payment transactions were confirmed as stolen, specifically:
- Full Name
- Email address
- Payment card number (PAN)
- Expiration date
- Card Security Code [CVV] - typically a 3 digit authorisation code written on the back of the debit\credit card
BA insists it did not store the CVV numbers, these are not allowed to be stored after payment card authorisation under PCI DSS. This suggests the card details may have been intercepted during the payment transaction, perhaps by a maliciously injected or compromised third party website plugin, as opposed to data theft from the database, as often seen with SQL injections attacks against web apps.
BA have published help and FAQs to anyone that is impacted by this data breach.
https://www.britishairways.com/en-gb/information/incident/data-theft/latest-information
British Airways is owned by IAG, their share price dropped by more than 4%, which equates to a £500m+ value loss in the company.
Update on the Attack Method (11 Sept 2018)
In a blog post RiskIQ researchers have claimed to have found evidence that a web-based card skimmer script was injected into the BA website, very similar to the approach used by the Magecard group, who are believed to be behind a similar attack against the Ticketmaster website recently. Web-based card skimmer script attacks have been occurring since 2015.
In this case, once the customer entered their payment card details and submitted the payment either on a PC or on a touchscreen device, the malicious script captured their data and sent it to a virtual (VPS) server hosted in Romania. The server was hosted on a domain called baways.com and was certified (https) by Comodo to make it look legit. The server domain was registered 6 days before the breach started, this obviously went undetected by BA's security, perhaps the rogue domain registration could have been picked up by a threat intelligence service.
Researchers have also claimed the BA website wasn't PCI DSS. They found 7 scripts running on the BA website, but crucially said the BA payment page wasn't isolating the card payments within an iframe, which would prevent third-party scripts (and XSS attacks) from being able to read the payment card form fields.
Bill Conner, CEO SonicWall said "Organizations and government entities carry a responsibility to consumers and civilians alike to guard their most valuable information at all cost. While the British Airways breach may not have been as detrimental as I’m sure its culprits would have liked it to be, it should serve as a wake-up call to CTOs, CIOs and CISOs. The fact is, it is early days, and the true damage done is yet to be seen. Personal information that does not change as easily as a credit card or bank account number drive a high price on the Dark Web. This kind of Personally Identifiable Information is highly sought after by cybercriminals for monetary gain. Companies should be implementing security best practices such as a layered approach to protection, as well as proactively updating any out of date security devices, as a matter of course."
British Airways is owned by IAG, their share price dropped by more than 4%, which equates to a £500m+ value loss in the company.
Update on the Attack Method (11 Sept 2018)
In a blog post RiskIQ researchers have claimed to have found evidence that a web-based card skimmer script was injected into the BA website, very similar to the approach used by the Magecard group, who are believed to be behind a similar attack against the Ticketmaster website recently. Web-based card skimmer script attacks have been occurring since 2015.
In this case, once the customer entered their payment card details and submitted the payment either on a PC or on a touchscreen device, the malicious script captured their data and sent it to a virtual (VPS) server hosted in Romania. The server was hosted on a domain called baways.com and was certified (https) by Comodo to make it look legit. The server domain was registered 6 days before the breach started, this obviously went undetected by BA's security, perhaps the rogue domain registration could have been picked up by a threat intelligence service.
Researchers have also claimed the BA website wasn't PCI DSS. They found 7 scripts running on the BA website, but crucially said the BA payment page wasn't isolating the card payments within an iframe, which would prevent third-party scripts (and XSS attacks) from being able to read the payment card form fields.
Bill Conner, CEO SonicWall said "Organizations and government entities carry a responsibility to consumers and civilians alike to guard their most valuable information at all cost. While the British Airways breach may not have been as detrimental as I’m sure its culprits would have liked it to be, it should serve as a wake-up call to CTOs, CIOs and CISOs. The fact is, it is early days, and the true damage done is yet to be seen. Personal information that does not change as easily as a credit card or bank account number drive a high price on the Dark Web. This kind of Personally Identifiable Information is highly sought after by cybercriminals for monetary gain. Companies should be implementing security best practices such as a layered approach to protection, as well as proactively updating any out of date security devices, as a matter of course."
03 September 2018
Cyber Security Roundup for August 2018
The largest data breach disclosed this month was by T-Mobile, the telecoms giant said there had been "unauthorised access" to potentially 2 million of their 77 million customer accounts. According to the media, a hacker took advantage of a vulnerability in a T-Mobile API (application programming interface). It was a vulnerable API used by Air Canada mobile App which was also exploited, resulting in the compromise of 20,000 Air Canada customer accounts. Air Canada promptly forced a password change to all of its 77 million customer accounts as a result, however, the airline faced criticism from security experts for advising a weak password strength. Namely, a password length of 8, made up of just characters and digits. Both of these hacks underline the importance of regularly penetration testing Apps and their supporting infrastructure, including their APIs.
Hackers stole up to 34,000 Butlin guest records, reportedly breaching the UK holiday camp firm through a phishing email. Dixons Carphone upped the estimated number of customer records breached in a hack last year from 1.2 million to 10 million, which includes 5.9 million payment cards. There was no explanation offered by Dixons to why it had taken so long to get a grip on the scale of the data breach, which was reported as occurring in July 2017.
Huawei continues to face scrutiny over the security of their products after the UK National Cyber Security Centre (NCSC) issued a warning about using the Chinese tech manufacturing giant's devices in a security report. Huawei recently took over from Apple as the world's second largest provider of smartphones. A 16 year old Australian 'Apple fanboy' found himself in court after hacking into Apple's network.
On the international scene, Microsoft announced it had thwarted Russian data-stealing attacks against US anti-Trump conservative groups, by taking down six domains which hosted mimicked websites, which were likely to be used in future phishing campaigns. The Bank of Spain's website was taken out by a DDoS attack, and a Chinese Hotel Group's 140Gb customer database was found for sale on the dark web. The PGA golf championship was hit by a ransomware, and the FBI arrested three key members of the notorious FIN7 hacking group, the group is said to be responsible for stealing millions of credit card and customer details from businesses across the world.
On the personal front, the EC-Council confirmed my Computer Hacking Forensic Investigation (CHFI) certification had been renewed until 2021. I dropped into B-Sides Manchester this month, the highlight was a demonstration of a vulnerability found by Secarma researches, namely a PHP flaw which places CMS sites at risk of remote code execution.
There was plenty of critical security patches released by the usual suspects, such as Microsoft, Cisco, and Adobe, the latter firm released several out-of-band patches during August. A critical update was released for Apache Struts (popular web server) and a reminder that Fax machines and all-in-one devices network devices could be used as a way into corporate networks by hackers.
Finally, there were a couple of interesting cybercrime articles posted on the BBC's news website this month, Cyber-Attack! Would your firm handle it better than this? and Unpicking the Cyber-Crime Economy
NEWS
Hackers stole up to 34,000 Butlin guest records, reportedly breaching the UK holiday camp firm through a phishing email. Dixons Carphone upped the estimated number of customer records breached in a hack last year from 1.2 million to 10 million, which includes 5.9 million payment cards. There was no explanation offered by Dixons to why it had taken so long to get a grip on the scale of the data breach, which was reported as occurring in July 2017.
Huawei continues to face scrutiny over the security of their products after the UK National Cyber Security Centre (NCSC) issued a warning about using the Chinese tech manufacturing giant's devices in a security report. Huawei recently took over from Apple as the world's second largest provider of smartphones. A 16 year old Australian 'Apple fanboy' found himself in court after hacking into Apple's network.
On the international scene, Microsoft announced it had thwarted Russian data-stealing attacks against US anti-Trump conservative groups, by taking down six domains which hosted mimicked websites, which were likely to be used in future phishing campaigns. The Bank of Spain's website was taken out by a DDoS attack, and a Chinese Hotel Group's 140Gb customer database was found for sale on the dark web. The PGA golf championship was hit by a ransomware, and the FBI arrested three key members of the notorious FIN7 hacking group, the group is said to be responsible for stealing millions of credit card and customer details from businesses across the world.
On the personal front, the EC-Council confirmed my Computer Hacking Forensic Investigation (CHFI) certification had been renewed until 2021. I dropped into B-Sides Manchester this month, the highlight was a demonstration of a vulnerability found by Secarma researches, namely a PHP flaw which places CMS sites at risk of remote code execution.
There was plenty of critical security patches released by the usual suspects, such as Microsoft, Cisco, and Adobe, the latter firm released several out-of-band patches during August. A critical update was released for Apache Struts (popular web server) and a reminder that Fax machines and all-in-one devices network devices could be used as a way into corporate networks by hackers.
Finally, there were a couple of interesting cybercrime articles posted on the BBC's news website this month, Cyber-Attack! Would your firm handle it better than this? and Unpicking the Cyber-Crime Economy
NEWS
- T-Mobile Breach Affects Two Million Customers
- Air Canada Mobile App Breach Affects 20,000 People
- Microsoft takes down 'Russian political Hackers
- Dixons admits Data Breach now Affects 10 million
- Butlin's says Guest Records may have been Hacked
- Huawei set to face even more scrutiny from UK Security Forces
- Reddit user data compromised after 'serious’ Hack
- Instagram Hack sees accounts replaced with film stills
- UK Universities among 76 targeted by Hackers
- Bank of Spain hit with DDoS Attack
- Chinese Hotel Group leak of Millions of Guests’ Data
- Reported Data Breaches up 160% since GDPR
- US warns of Supply Chain Cyber-Attacks
- PGA Championship hit by Ransomware Attack
- Teenage fan Hacks into Apple network
- NIST issues Guidance for Protecting Medical IoT devices
- FBI arrests key members of 'prolific’ FIN7 Cyber Crime Group
- Microsoft Patches 60 Vulnerabilities for Windows, IE\Edge, Office, .NET, Exchange, SQL, Chakra and Adobe
- PHP flaw places CMS sites at risk of remote code execution
- Adobe Releases Important Fixes for Flash Player
- Adobe Releases Critical Fixes for Acrobat and Acrobat Reader
- Adobe pushes out ‘out-of-band’ Critical Updates for Photoshop CC
- Adobe issues ‘out of band’ Patch for Creative Cloud Desktop Application
- Cisco Patches DoS-related flaws in AsyncOS, Unified Comms Manager (CUCM, IM, and P) and ASA
- 'Foreshadow' attack affects Intel chips
- Fax machines and all-in-one devices could be used by Hackers to Infiltrate Networks
- Security update issued after Critical RCE vulnerability found in the core of Apache Struts
- Cyber fall-out of nation-state conflicts extends beyond politics
- Experts warn of increase in Phishing Attacks targeting Cryptocurrency
- Latest Mirai variant leverages open source project for cross-platform infections
- AdvisorBot Downloader in Malware Campaign targeting Hotels, Restaurants, and Telecoms
- Researchers find new POS malware with no data exfiltration capabilities
- CrowdStrike: Global Supply Chain Survey, two-thirds of organisations attacked
- Mimecast ESRA Report: Email attacks on the rise, say 80% of Businesses
- Data Leakage Prevention (DLP) – ISF Briefing Paper
- Cyber-Attack! Would your firm handle it better than this?
- Unpicking the Cyber-Crime Economy
- Cyber fall-out of nation-state conflicts extends beyond politics
