- Educate all business staff about dangers and latest attack methods, particularly ensuring they aware of targeted scam emails (spear phishing). Cyber criminals are increasingly targeting individual business staff members, typically those with finance responsibilities, by crafting highly convincing emails using information about the business, its staff and its suppliers. These scam emails once responded to, will typically try to convince (social engineer) individual staff members to arrange a bank transfer or payment to a bogus account operated by the cyber criminals
- Keep all Servers, PCs, Laptops, Tablets and Smart Phones operating systems and applications updated (security patching). Out of date software is vulnerable and commonly exploited by malware and hackers.
- Business staff should use unique passwords with each third party/online service used by the business. Ensuring passwords are complex and changed every 90 days. Where possible use mutli-factor authentication (I.e. password + hardware token or text message confirmation). Cyber criminals know many people use the same email and password combination across multiple websites, so when they obtain one credentials combination, usually via a third party website hack, the database of which are often dumped onto the darkweb, cyber criminals try the same stolen email and password combinations to attempt to access further online services, with the intent of stealing personal data and money.
UK cybersecurity analysis, operational resilience, control assurance, AI security, and evidence-based governance from experienced practitioners and guest contributors.
21 December 2016
How to Protect your Business from Cyber Crime
Today I was quoted in the Focus Training's Blog. An 'Ask the Experts' piece on 'How to Protect your business from Cyber Crime', my advice was as follows.
20 December 2016
UK Identity Fraud on the Rise
UK identity fraud is on the rise according to the latest research by Equifax. The data shows UK ID crime is going up within all age groups, with those living in the London and Manchester areas increasingly the most likely to become victims of ID fraud. Equifax has asked me to share the following infographic on their research, which includes good advice to stay protected.
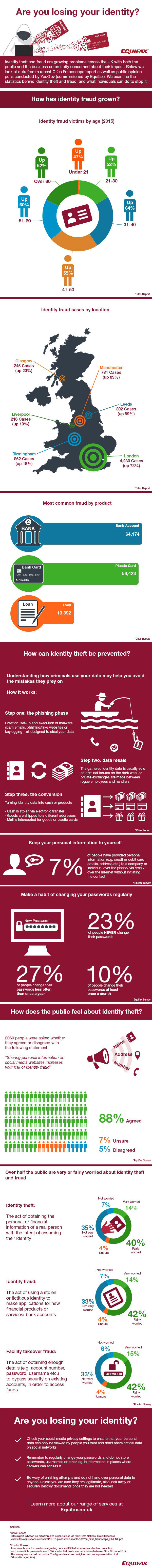
Are you losing your identity? We look at the growth of identity fraud and what can be done about it
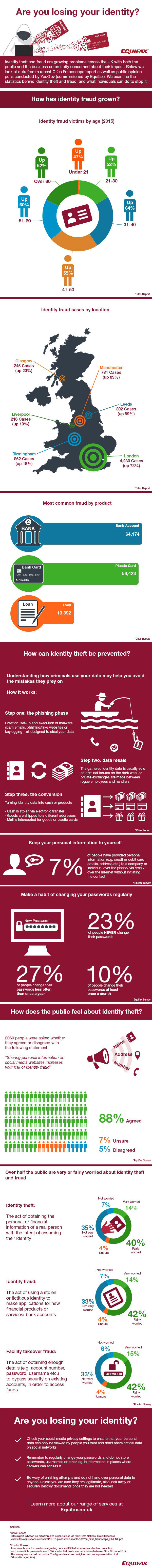
Are you losing your identity? We look at the growth of identity fraud and what can be done about it
15 December 2016
Yahoo's Mind-blowing One Billion Data Theft Hack
Just over three months ago I posted about Yahoo, The Largest Data Breach in History...so far. It was apt I added "so far" in the post title as in the early hours today, Yahoo announced an even more mind-blowing data theft hack of over One Billion Yahoo user accounts.
If you are a concerned Yahoo email account holder
The latest reports say that Yahoo lost data for more than one billion users back in August 2013 and that the data is suspected to contain names, email addresses, hashed passwords, security questions and associated answers. In addition, Yahoo has stated that the attackers have accessed Yahoo proprietary code used to generate cookies for user access without credentials.
This breach raises a number of questions, including: Why did it take so long to identify and notify authorities about it? What are the implications for Yahoo users? What might this mean for Yahoo going forward?
Yahoo appears to have been informed by law enforcement that the breach may have occurred, indicating that its internal detective controls have been, and may continue to be, inadequate. This is reinforced by a statement from Bob Lord (Yahoo's CISO) who stated "we have not been able to identify the intrusion associated with this theft." (https://yahoo.tumblr.com/post/154479236569/important-security-information-for-yahoo-users).
Although Yahoo claims that this notification is distinct from the 2014 breach (reported in September 2016), it raises questions as to why this more significant breach was not identified during earlier investigations. Forensic investigations may have been either too focussed on the 2014 breach, or incomplete, preventing identification of this earlier and more significant breach. To add balance to this argument, it should be stated that it is not clear at this time if the breached systems were related, however following the 2014 breach, Yahoo should certainly have considered further investigations to identify if any wider breaches had occurred.
So what are the implications for Yahoo users? Considering that this breach constitutes approximately one-third of Yahoo’s user base, it would be a fair assumption for all Yahoo users that their accounts have been compromised. The data set reported to be compromised includes both username and passwords, and whilst the passwords are reportedly hashed, the weak algorithm in use leaves them wide open to abuse (see our earlier blog post on password hashing - https://www.cyberis.co.uk/2012/06/adding-pinch-of-salt.html)
Cyberis advises Yahoo users, and users of related services such as Flickr and Tumblr, to change their passwords with immediate effect. If you have used your Yahoo password with any other service, you should also change these passwords. If you have registered for a website using a Yahoo email account, you should also consider resetting your password for these services, especially if you haven't used them for some time. Password reset services often use email addresses to manage a password change or forgotten password function. Anyone with access to the breached data could have potentially used this information to access any site associated with your Yahoo email account.
Given that Yahoo has announced that proprietary data was accessed, the breach is currently assumed to extend to Yahoo internal systems. This could suggest a highly skilled and motivated adversary, potentially even a state-sponsored hacking group. Access to millions of email accounts would be a clear motivation to many different threat actors of course, including foreign intelligence services and governments. We fully expect that further information about the extent of the breach will be released in the near future, but in the meantime, it’s certainly not looking good for Yahoo.
If you are a concerned Yahoo email account holder
1. Reset your Yahoo account password, make sure your old Yahoo passwords are not used on any other of your online accounts
2. Change your Security Questions and Answers on all accounts with same Q&A as Yahoo, you might have to make up false answers only you know to ensure safety
3. Be extra vigilant, especially with signs of any access to your email account, and receiving scam phishing emails
Mark Crowther, Associate Director at Cyber Security Specialists Cyberis (www.cyberis.co.uk), has some interesting thoughts on the latest breach at Yahoo, raising serious questions about the company's historical and ongoing security programme. The following are his views.
The latest reports say that Yahoo lost data for more than one billion users back in August 2013 and that the data is suspected to contain names, email addresses, hashed passwords, security questions and associated answers. In addition, Yahoo has stated that the attackers have accessed Yahoo proprietary code used to generate cookies for user access without credentials.
This breach raises a number of questions, including: Why did it take so long to identify and notify authorities about it? What are the implications for Yahoo users? What might this mean for Yahoo going forward?
Yahoo appears to have been informed by law enforcement that the breach may have occurred, indicating that its internal detective controls have been, and may continue to be, inadequate. This is reinforced by a statement from Bob Lord (Yahoo's CISO) who stated "we have not been able to identify the intrusion associated with this theft." (https://yahoo.tumblr.com/post/154479236569/important-security-information-for-yahoo-users).
Although Yahoo claims that this notification is distinct from the 2014 breach (reported in September 2016), it raises questions as to why this more significant breach was not identified during earlier investigations. Forensic investigations may have been either too focussed on the 2014 breach, or incomplete, preventing identification of this earlier and more significant breach. To add balance to this argument, it should be stated that it is not clear at this time if the breached systems were related, however following the 2014 breach, Yahoo should certainly have considered further investigations to identify if any wider breaches had occurred.
So what are the implications for Yahoo users? Considering that this breach constitutes approximately one-third of Yahoo’s user base, it would be a fair assumption for all Yahoo users that their accounts have been compromised. The data set reported to be compromised includes both username and passwords, and whilst the passwords are reportedly hashed, the weak algorithm in use leaves them wide open to abuse (see our earlier blog post on password hashing - https://www.cyberis.co.uk/2012/06/adding-pinch-of-salt.html)
Cyberis advises Yahoo users, and users of related services such as Flickr and Tumblr, to change their passwords with immediate effect. If you have used your Yahoo password with any other service, you should also change these passwords. If you have registered for a website using a Yahoo email account, you should also consider resetting your password for these services, especially if you haven't used them for some time. Password reset services often use email addresses to manage a password change or forgotten password function. Anyone with access to the breached data could have potentially used this information to access any site associated with your Yahoo email account.
Given that Yahoo has announced that proprietary data was accessed, the breach is currently assumed to extend to Yahoo internal systems. This could suggest a highly skilled and motivated adversary, potentially even a state-sponsored hacking group. Access to millions of email accounts would be a clear motivation to many different threat actors of course, including foreign intelligence services and governments. We fully expect that further information about the extent of the breach will be released in the near future, but in the meantime, it’s certainly not looking good for Yahoo.
01 December 2016
Cyber Security Roundup for November 2016
Several major UK household brands made the headlines for wrong reasons following cyber attacks in October. Tesco Bank refunded £2.5 million to over 20,000 of its customers after Tesco Bank account credentials were hacked and account funds were stolen. Mobile giant ‘Three’ said 6 million of its customer’s personal data records could be at risk after hundreds of new mobile phones were stolen following the hack of a Three employee account. The National Lottery disclosed 26,500 of its online customer accounts had been accessed by hackers, leading to three arrests. Elsewhere a 17 year old pleaded guilty to taking part in the recent TalkTalk hack.
The next evolution of ransomware has arrived with a new variant called Ransoc, and it's pretty nasty. The malware scans internet history, social media accounts, Skype and photos, and then uses any found illegal, embarrassing and sensitive information to threaten the victim’s reputation should a payment not be sent.
It turns out locked computer desktops aren’t as safe as you might think after a security researcher Samy Kamar released details of new attacking method called PoisonTap. Samy is famous for hacking MySpace with a worm way back in the day, I had the pleasure of meeting him a few years ago - An Evening with Samy, creator of the Samy MySpace Worm. In simple terms PoisonTap works by plugging a £4 Raspberry Pi Zero computer configured with hacking tools into a USB port, forcing the USB port to act as a network port, the tool is able to eavesdrop non-encrypted network traffic and steal web sessions from web browser sessions running in the background on PCs and Apple Macs, despite the desktop being locked with password protection. Samy released the source code for PoisonTap on Github, and I intend to create a PoisonTap tool for myself in the next few days.
News
- Tesco Bank Hack: £2.5m refunded to 20,000 Customers
- Three Data Breach Cyber Hack: Six Million Customers Data at Risk
- National Lottery Hack: 26,500 Players' Online Accounts Accessed
- Financial Conduct Authority rapped for Lack of Cyber Experts on Board
- Lincolnshire NHS Trust Operations cancelled after Cyber Attack
- Capgemini Leaks 780,000 Michael Page Job Candidate CVs
- UK iPhone users hit by large scale Smishing Campaign
- 17-year-old pleads guilty to offences linked to TalkTalk Hack
- European Commission gets DDoSed
- Hackers hit San Francisco transport Systems
- Bruce Schneier: ‘The internet era of fun and games is over'
- Microsoft release 6 Critical Patches for Windows, Edge, IE, Video Control & Flash
Awareness, Education and Intelligence
- NIST Releases CyberSecurity Guide for Small Businesses
- New Ransomware Variant Extorts your Reputation rather than Money
- PoisonTap: £4 Tool which can hack locked PCs via a USB Port
- YouTubers sell Phishing Kits in Plain View
- Cerber Ransomware: Now with Database Encryption
- Facebook spam caught delivering Locky Ransomware